In May of this year, members of the CyberSaint team attended the National Defense Industrial Association New England Chapter’s annual forum. This year, the topic was DFARS Cybersecurity 2.0: The Year of Continuous Monitoring, spotlighting the GDPR. The goal of the forum was to clear the air about the DFARS 252.204-7012 requirements placed on Department of Defense (dod) contractors and the supply chain, including defense manufacturers and all those who sell to the DoD.
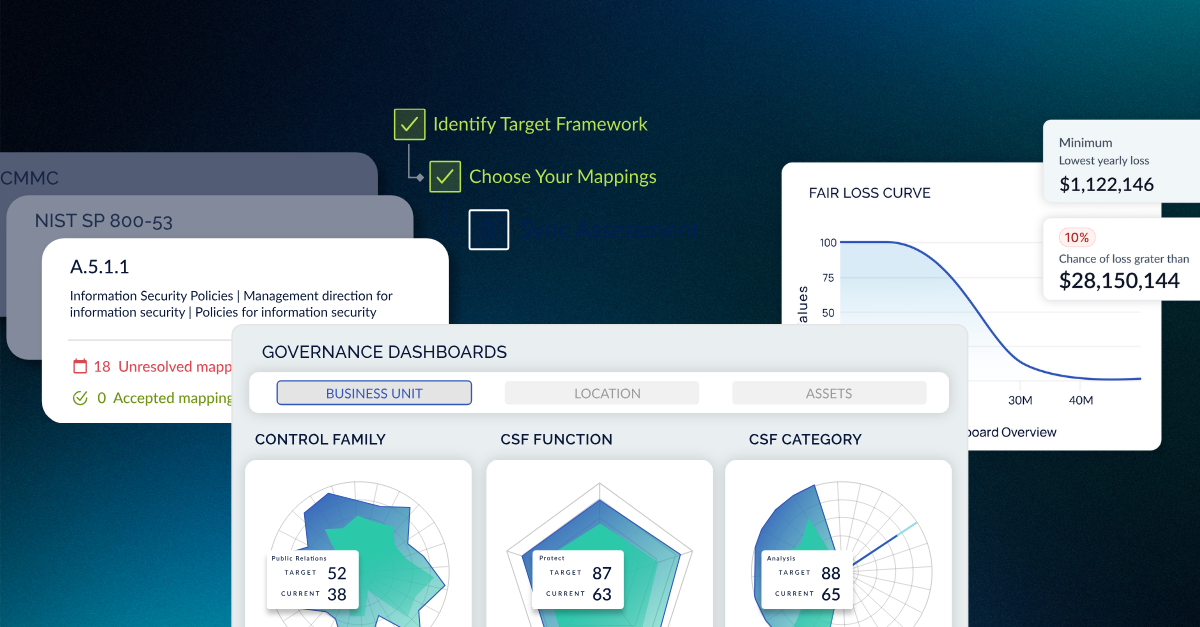
DFARS has taken its toll on some companies that only generate a small portion of their revenue through selling to the DoD. Some of these companies have decided to get out of that business altogether because their revenue generation from that channel is small enough that the cost of remediation to comply with the DFARS regulation versus the revenue generated doesn’t align. Others who have built their businesses upon selling to the DoD or who sell a reasonable portion of their product or service to the DoD have decided to invest in cybersecurity measures to prove adequate security per the NIST Special Publication 800-171 requirements. We’ve helped both kinds of organizations make the decision because CyberStrong provides the lowest cost option to measure, track, and report compliance rendition steps and an AI-optimized cost-weighted remediation plan to use moving forward. Whatever you may be contemplating, there are options and teams out there that you can use to help guide your decision-making process.
The Defense Contract Management Agency Clears the Air on DFARS
At the DFARS Cybersecurity 2.0 Forum, hosted by Raytheon Integrated Systems at its Freedom Theater, the first topic that we took heavy note of was that concerning changes within the Department of Defense and their stand on DFARS compliance for this year. According to the Defense Contract Management Agency (DCMA) representatives, with cyberattacks costing companies $400B each year and incidents surging 38% just since 2014, the focus on cybersecurity has never been greater. Aside from the Primes, the DCMA is the group tasked with asking companies and contracting officers who fall under DFARS for their System Security Plans (SSP) and Plans of Action and Milestones (POAM) to assess their adherence with the NIST SP 800-171 controls.
Most of those who have researched or know about the Defense Federal Acquisition Regulation Supplement (DFARS) have heard of “adequate security” at least once. According to the DoD, any system within an organization that stores, processes, or transmits Controlled Unclassified Information, or Controlled Defense Information, is required to prove adequate security on that system in accordance with controls listed in NIST SP 800-171. These controls are best-practice controls that double as data protection controls as well, in a lot of cases, not just cybersecurity. The DCMA noted that the rumor that NIST SP 800-171 will become a Federal Government Acquisition Regulation (FAR) is true and that the realization of this idea will likely happen before the end of 2018.
One of the concerns that came from those in the audience who actually had/have to focus on and adhere to NIST 800-171 is the idea that the regulatory guidance is too vague - there is ambiguity on the edges as they scope their environments - what is CUI/CDI really? When is the data potentially destructive to the DoD if beached? The DCMA noted that this input, one they were already aware of from others, is informing how they approach the FAR rule that will cover many more organizations than just the DoD and supply chain.
When Should 252.204-7012 Flow Down to Subcontractors?
The DFARS flow-down applies to organizations storing, processing, or transmitting CUI/CDI. Even the small organizations that only generate a small portion of their revenue from DoD business fall under the flow-down. It’s not about revenue from Department of Defense- related customers or the site of your company - it’s all about whether your product or service is used by the Department of Defense or not, and if even your dod contracts and the RFPs associated with your bids could give cybercriminals any indication of Department of Defense-related activity. Another key element of the regulation is that those who fall under it must use the Web Portal provided by the DoD to submit and report cyber incidents. CyberSaint’s team highly recommends not using email - it increases the risk that information about your breach could get out.
Demonstrating Implementation of 800-171 Compliance
The three elements of DFARS compliance, and proving adherence to the reg were made clear at the forum by the Defense Contract Management Agency (DCMA):
- Plan of Action and Mitigations/Milestones (POAM)
- System Security Plan (SSP)
- The ability to have these documents, with the most recent data, read at any time as Fed agencies will request SSP in solicitation or with a proposal, as well as the POAM
DFARS Audits and Assessments
The DCMA plans to ask for the POAM and SSP and see if organizations are making the right decisions and progressing toward full compliance. The DCMA does not plan to do a full assessment against the NIST Sp 800-171 controls. However, they can if they feel it’s necessary to move forward. The Major elements of the DCMA and how they are approaching your compliance are that they will:
- Review of System Security Plan (SSP)
- Assess or request an assessment of the contractor’s internal information system
- Since the DFARS clause is in most contracts now and all new contracts, they will review the contract accordingly
- Could you decide to track plans of implementation and adherence to your POAM





.png)
.png)
.png)
%201.png)
.png)