In the ever-expanding digital landscape, businesses continually embrace many technologies to stay competitive and agile. However, this rapid adoption often leads to a complex web of disparate tools, giving rise to what is known as technology sprawl. As organizations grapple with the challenges posed by this intricate network of technologies, the need for robust cyber risk management has never been more critical.
This blog post delves into the intricacies of technology sprawl and its profound impact on cybersecurity. We will explore how the traditional approach of relying on endpoint solutions is no longer sufficient in the face of evolving threats. Instead, a paradigm shift towards comprehensive cyber risk management solutions is underway, reshaping how organizations identify threats and mitigate cyber risks in real time. Join us on this journey as we unravel the complexities of the modern technological landscape and examine the transformative evolution of cyber risk management tools.
The Domino Effect of Technology Sprawl
A growing range of specialized tools are available to help organizations mitigate cyber risks. These solutions encompass threat intelligence, vulnerability management, SIEM tools, and AI-based cybersecurity solutions. Technology sprawl results in a diverse hardware, software, and services ecosystem sourced from different vendors. This diversity can lead to interoperability issues, as various technologies may not seamlessly integrate. Cyber risk management strategies must contend with this complexity, as interoperability challenges can create security gaps and vulnerabilities that attackers may exploit.
A sprawling technology landscape inherently expands the attack surface for potential cyber threats. With a myriad of interconnected devices, applications, and platforms, the attack vectors multiply, providing adversaries with more opportunities to exploit vulnerabilities. Cybersecurity operations must constantly adapt to monitor and defend against a broader range of potential entry points.
Technological and solution sprawl have made the job of CISOs and security professionals particularly hard. Each enterprise’s attack surface is unique, and it changes rapidly. Small changes or oversights can lead to significant risks in a rapidly evolving threat landscape.
The proliferation of cyber solutions can be perplexing, even for experienced professionals. Not all solutions are of equal value, and a universal approach may not be applicable. Several solutions lack flexibility and fail to take into account existing business processes. Legacy products demand extensive time for configuration and training, often relying on costly services. Those opting for more agile capabilities often need help integrating new offerings, falling short of achieving the intended results.
Technology sprawl often gives rise to shadow IT, where employees independently adopt and use applications without formal approval from the IT department. Unapproved apps can introduce security risks, as they may not adhere to the organization's cybersecurity policies. Identifying and securing these applications becomes a significant challenge for cybersecurity teams.
The fast-paced evolution of technology compounds the challenges for cybersecurity operations. New technologies emerge regularly, and existing ones undergo frequent updates. Keeping pace with these changes is essential for maintaining a secure environment. However, it requires continuous training, monitoring, and adaptation, adding another layer of complexity to cybersecurity efforts.
Lack of Transparency in Cyber Risk Management Tools
In addition to the flood of several-point solutions come varying claims of the most advanced and accurate cyber risk score. Security professionals should tread cautiously if their tool cannot transparently state how they calculate their risk data.
Transparency is critical to cyber risk operations. Professionals should not leverage models that do not explicitly state how the data has been used to calculate risk scores. For CISOs, this means they cannot defend their cyber risk data during presentations simply because they need to know how the scores were calculated.
Many cyber risk management tools, such as service providers, legacy vendors, and specific corporate risk and compliance practices, have adopted a short-term fix. The data used for cybersecurity risk assessments plays a crucial role. While assessment methodologies may be robust, relying on a six-month-old assessment is ineffective. Given the rapid changes in environments and threats, data quality becomes paramount. It is widely acknowledged in cyber that relying on outdated data and spreadsheets for cyber risk assessments has existed for too long. The swift aging of data is a well-known challenge that the industry collectively recognizes.
The most forward-thinking organizations tackle this issue through strategic partnerships and a customized development approach. Conversely, the same cannot be said for prominent GRC software solutions, as they have minimal flexibility in their risk approach and reuse outdated data that holds minor to no value.
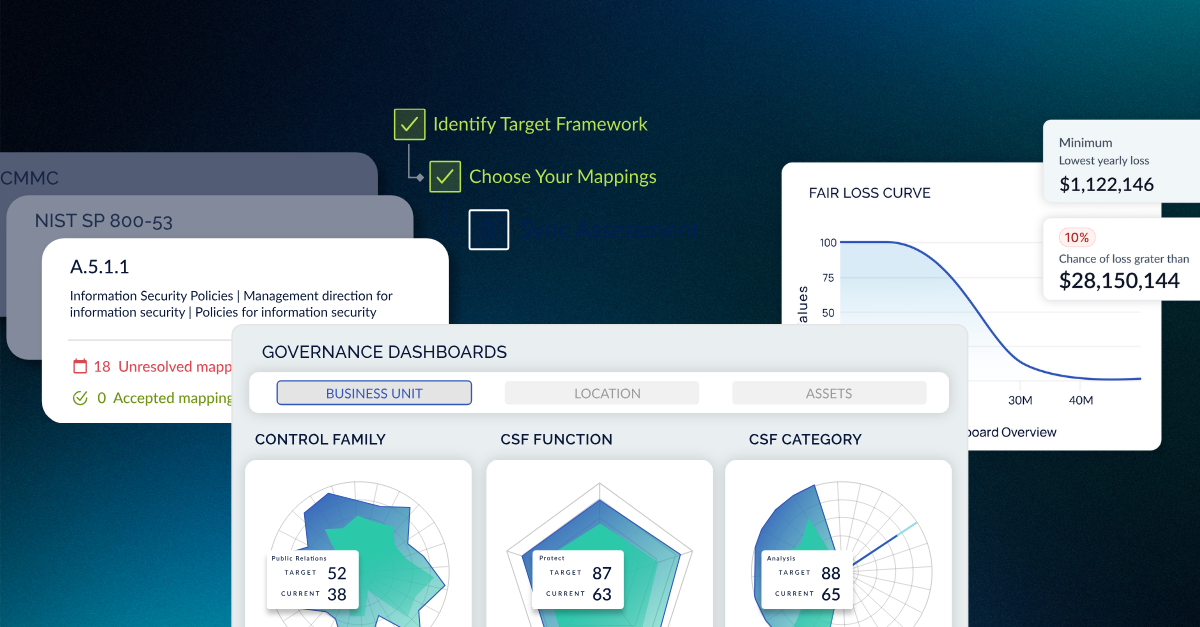
The New Frontier for Cyber Risk Management Tools
The era of cybersecurity risk management is here. It’s time to relate security operations to risk and vice versa. Through the many data breaches and new regulations, it’s clear that the industry recognizes the importance of cyber risk in security operations and compliance. And with this moment comes the understanding that cybersecurity is everyone’s responsibility. This means that Boards and C-suite leaders must understand cyber, and security leaders must step up to the plate and deliver defensible metrics—no more excuses of cyber being overly technical, tangential risk scores, or old spreadsheets.
Comprehensive cyber risk management is imperative for the organization to move forward effectively. Compounded with the scrutiny of the new SEC cybersecurity rules, security professionals need to deliver on transparency and accuracy, and two ways to do that are to shed disparate tools and leverage automation. By doing so, teams will be relieved of managing several applications' nuances and challenges. They will be empowered to do more within cyber operations by leveraging a cyber risk management platform that supports end-to-end processes.
Cyber risk management platforms that leverage automation give security professionals the agility and flexibility to manage several operations unique to the organization and scale operations with the business. Additionally, automated solutions account for the rapidly shifting cyber landscape. This ensures that security professionals deal with the most up-to-date data and can defend their metrics.
Wrapping Up
As the era of cybersecurity risk management unfolds, the industry recognizes the pivotal role of cybersecurity in risk and compliance. The call to action is clear: Boards, C-suite leaders, and cybersecurity professionals must collaborate to manage cyber risk.
The importance of a robust cyber risk management platform becomes evident in the face of potential SEC scrutiny. Such platforms, leveraging automation, empower security professionals to navigate the complexities of the modern cyber landscape. The future of effective cyber risk management lies in agility, flexibility, and embracing transformative technologies to secure organizations in an ever-evolving digital landscape.
Meet with the CyberSaint team to learn more about our comprehensive approach to cyber risk management.





.png)
.png)
.png)
%201.png)
.png)