In our Integrating Governance Risk and Compliance series, CyberSaint leadership explores the process through which cybersecurity leaders can reconfigure their organizations to support the new paradigm of information security as a business function.
Risk management is fundamental to a cybersecurity program. Coupled with necessary compliance activities to support ongoing business operations, risk management centers upon identifying and working to remediate the risks associated with a given organization. Where ensuring compliance is the baseline that businesses in a specific industry or location must adhere to, risk management is where businesses must differentiate and determines where the risks specific to an organization lie. As more enterprises embrace digital technology, the relative importance of risk over compliance has grown; with the growing variety of technologies that organizations are adopting, baseline compliance is necessary, but still only a basic step to ensuring that the organization is secure.
The Importance of Risk Assessments
Almost all risk management frameworks require the consistent use of risk assessments. Whether NIST 800-30, FAIR, or even a three-by-three matrix - risk assessments are the foundation on which all approaches to risk management are built.
Choosing a risk assessment methodology comes down to what makes the most sense for your organization. My recommendation is to start general and then tailor based on your findings. Once your organization has a baseline, determining the best framework or combination of frameworks will become clearer. Remember, a risk assessment methodology should bring your organization closer to understanding the risks that are specific to strategic or business goals. It is far too easy to get lost in a methodology. As a math professor once said to me, “Don’t mistake the model for reality.” The point is to leverage a model or methodology to get a deeper understanding of reality. Resource decisions and risk appetite are much easier to handle if metrics are defensible and easy to understand.
Risk Management Frameworks
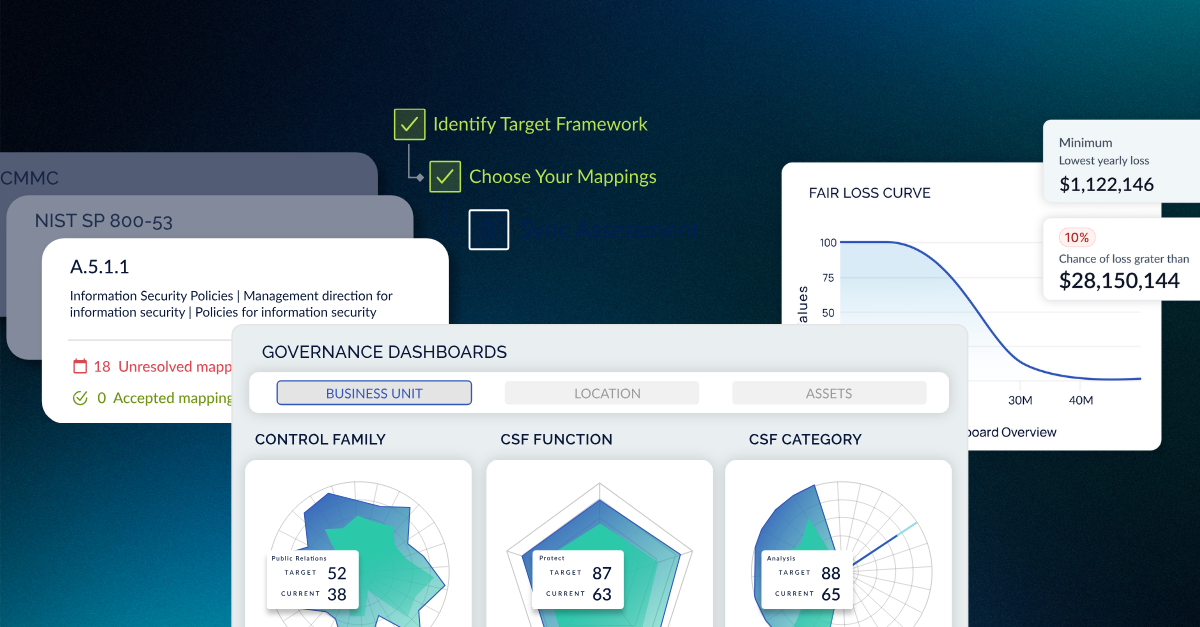
The primary mode of risk management in the context of integrated GRC activities is a risk management framework. Starting with risk assessments and then moving into how certain risks are addressed and what risk remediation activities are prioritized often starts with a framework. In most cases, an integrated GRC framework will use risk management as the foundation. In the case of the CyberStrong, and other integrated risk management platform and integrated GRC solutions, risk is baked directly into the assessment process. Assessing risk and compliance in tandem sheds light on both your organization's compliance stance while simultaneously illuminating risk remediation priorities.
Translating Cyber Risk to Stakeholders
Arguably, the most important aspect of risk management is leveraging information to improve the resiliency of the organization. For many business-side leaders, cyber risk is unknown. Yet, in today’s digital world, CEOs and Boards must have the ability to integrate cyber risk into the overall enterprise risk profile. This is where risk quantification becomes critical.
This is driving security leaders to examine various risk quantification methodologies. The goal is to match the proper methodology to specific business and reporting requirements, and to provide the most value. The optimal risk quantification method will ideally be based upon how senior management is used to seeing risk - business, operational, strategic - to help them roll cyber risk into that mix.
Risk Data Visualization
Finally, using an integrated view of risk helps both the remediation and communication to business leaders. Using the right mix of risk quantification breakdowns (threat type and business impact in the case of CyberStrong) helps contextualize technical risk metrics in a way that can both help technical leaders prioritize remediation activities, while also conveying the risk profile to non-technical stakeholders in a credible manner.
The Foundation To a Forward-Looking Cyber Program
While traditional GRC approaches are guided by checkbox compliance activities, integrating IT governance and risk management activities requires doing these activities in tandem. Given that organizations are unique and adopting myriad new technologies, customizing a risk management program to the enterprise--rather than to general compliance standards--is critical. Structuring goals around a deeper understanding of enterprise risk enables an organization to both prioritize specific risks and threats to the business, as well as convey that information to management in an actionable, credible manner. Integrating risk management and GRC tools begins with a paradigmatic shift in thinking, but doing so can yield substantial value to the security posture of the organization.





.png)
.png)
.png)
%201.png)
.png)