The incident response framework by the National Institute of Standards and Technology (NIST) is an impactful beginning for organizations looking to optimize their incident plan and management approach.
It all starts with establishing the capacity for incident response, including plans, procedures, and policies. To facilitate reporting, a structured team comprising IT personnel and third parties like media contacts and law enforcement should be responsible for such tasks.
Cybersecurity incidents have become a necessary evil for businesses that want to scale faster. There were 1,767 data breaches reported in the first half of 2021, exposing over 18.8 billion records. This spike is a stark increase from the same period a year earlier when malicious actors accessed 4.1 billion records.
Today, hackers deploy ever-changing tactics and sophisticated technology to steal valuable data from businesses. These organizations are left struggling to fend off cyber threats. No matter what they do, hackers are always a step ahead, as substantiated by the fact that enterprises with robust security measures often deal with data breaches.
It doesn't help that only 23% of surveyed businesses had cyber and incident response plans prepared in 2019, and the numbers haven't improved by much. Incident response plans help IT, and technical staff identify, respond to, and recuperate from network-related security incidents. The program addresses data loss, service outages, and cybercrime threatening daily work.
Creating a good incident response plan should include a course of action for multiple incidents. Some attacks may lead to massive data or network breaches, impacting your business for days or months. When a significant disruption occurs, your company must have a detailed, thorough incident response plan to assist IT staff in efficiently preventing, containing, and regulating the incident.
Critical Roles in an Incident Response Plan
Ensure the effectiveness of your incident response plan by working with a reliable team.
In enterprises, entire teams or full-time employees typically carry out the roles. But in smaller companies, these roles are filled by workers/teams with other full-time responsibilities, who also take part in the incident response procedure.
Here are the essential roles in an incident response team plan:
- Security Analysts - identify possible incidents, review alerts, and execute an initial study to comprehend an attack's scope
- Incident Response Managers - there should be at least two team members accountable for approving the incident response plan and coordinating activity when an event occurs.
- Threat Researchers - are responsible for providing contextual information regarding a threat, leveraging data from the web, security tools, threat intelligence feeds, etc.
- Third Parties - such as outsourced security services, lawyers, and law enforcement agencies.
- Other stakeholders - include board members, senior management, PR, HR, and senior security teams such as the Chief Information Security Officer (CISO).
Incident Response Plan Challenges
There are some common challenges and roadblocks encountered by CISOs when creating an incident response plan. Understanding these issues can provide valuable insights into improved incident management before they become major security concerns.
Having No Database Of Critical Assets
Not having a list or database covering critical assets is usually due to inefficient management procedures and processes. Not having your necessary assets' data documented decreases the ability to protect and safeguard them from potentially malicious actors.
Therefore, developing an inventory of all essential data and assets is imperative. Establishing proper list management processes, including reviews, storage, and updates, is also vital.
Insider Threats
The risk of effective insider exploits in a company increases if you don't have an insider threat program. The compromise or loss of critical assets, sensitive information, personally identifiable information (PII), and other essential assets from insider theft, fraud, and acts of terror may cause irreparable damage.
According to insider attack statistics from 2020, around 2,500 inside security breaches arise in the United States every day - almost one million every year. As a result, a formalized and well-implemented insider threat program has defined responsibilities and roles. The threat program should have thresholds to conduct inquiries, refer to investigators, and request prosecution.
Budgetary Constraints
One of the other challenges CISOs face in the planning of incident response strategy is that incidents and management plans are often difficult to implement and theorize because companies lack the effective allocation of the budget for IT.
According to Forbes, CISOs should anticipate a halt in progress for IT budgets internationally. Additionally, The Wall Street Journal reports that reducing budgets for an organization's IT spending is not being leveraged for incident management. Instead, AI and cloud services are the utmost priority.
Four Phases of the NIST Incident Response Plan
NIST provides four main phases of a standard incident response plan. It is imperative to recognize that post-incident and preparatory activities are also unequivocally essential. NIST highlights both types of actions in their provided outline.
Here are the main phases of the NIST incident response plan:
Preparation
To accurately prepare for handling incidents, it is essential to compile a proper list of IT-related assets like servers, endpoints, and networks, recognizing their importance and the ones that hold sensitive or critical data.
Set up a baseline of everyday activities. Determine the types of security-specific events you should investigate and create comprehensive response guides for different incident types.
Detection and Analysis
Detection includes data collection from security tools, IT systems, publicly accessible information, people outside and inside the organization, and recognizing precursors (indications that an event may happen down the road) and pointers (data demonstrating that an attack is happening now or has happened).
Moreover, the analysis covers determining an average or baseline activity for the impacted systems, seeing how and if they deviate from standard behavior, and co-relating events.
Containment, Eradication, and Recovery
Containment aims to prevent attacks before they overwhelm the resources. Your company's containment tactic depends on the damage level of the incident, the requirement to keep essential services available to customers and employees, and the duration - a temporary resolution for a few days, weeks, or hours, or a perpetual solution.
Then, once your team effectively contains the issue in the recovery and remediation stage, it is essential to eradicate all incident elements from the setting. This step may include finding all affected hosts, resetting or closing passwords for ruptured user accounts, and removing malware.
Ultimately, once you eliminate the threat - recover normal operations, restore systems as quickly as possible, and implement steps to ensure the same assets aren't compromised again.
Post-Incident Activity
An integral part of the incident response methodology of NIST is learning from past incidents with incident analysis.
You need to look at the entire incident process with a meek but critical eye to find areas for improvement. Include those improvement pointers in your documentation.
Incident Response Life Cycle Of NIST
NIST outlines a four-step process for incident response. This process emphasizes that incident response isn't a linear activity that begins when your team recognizes an incident and ends with elimination and recovery.
Instead, incident responses are cyclical activities. Your team should continuously improve response plans to defend the organization more effectively. After each incident, there should be considerable effort to investigate and document what happened throughout the incident, review earlier stages, and manage and prepare better for analysis and detection of future incidents.
Also, there is a feedback loop from the last step, ranging from containment, and eradication, to detection and analysis — various parts of an attack aren't fully comprehended at the recognition stage. They are only exposed when an incident responder "enters the scene." These learnings can help your team identify and analyze attacks expansively the next time around.
Models For Incident Response Team
Essentially, NIST offers and outlines three models aimed at incident response teams.
- Distributed: Various incident response teams are responsible for particular physical locations such as a branch office, a part of the IT-related infrastructure, or a department.
- Coordinated: Incident response teams work collectively with dispersed incident response teams without authority over them. Here the central team offers assistance and acts as a knowledge center with cortical, organization-wide, and complex, critical incidents.
- Central: This centralized body manages and supervises the organization's incident response.
In each of these models mentioned above, the teams can include employees, fully outsourced or partially outsourced. Employees can also be part or full-time.
How to Select A Team Model
No process is foolproof. The threat landscape is ever-changing, so your incident response plan will naturally require an update.
Answer the following questions to select the most suitable incident response model for your teams:
- Should staff be full-time or part-time?
- Should the incident response be available 24/7?
- How much will be the costs of the incident response team?
- Does staff need to be security experts?
How To Establish an Incident Response Unit
The Incident Response Guide by NIST provides standard instructions to organize and operate an incident response unit.
Establish A Proper Incident Response Competence
Even if your company is small, taking incident response planning seriously and establishing a proper response body is paramount. It is essential to define this team and give it the responsibility and authority to radically improve your company's capability to address cyberattack strikes.
Formulate Incident Response Policies
Formulating policies is integral to your response plan. These policies should include the company framework that specifies security incident considerations, who is liable for incident response, documentation, reporting requirements, and roles and responsibilities.
Define the Plan Accurately
As per NIST methodology, incident response plans are implemented when an incident occurs and act as a roadmap for the enterprise's incident response strategy. This strategy should include long-term and short-term goals, job and training requirements, and metrics for measuring success for incident-related response roles.
Create Incident Response Processes
The defined processes are the comprehensive steps that teams can use to respond to an incident. Your team should base these steps on the plan and policy for the incident response that addresses all four phases – preparation, detection and analysis, containment, eradication and recovery, and post-incident activity.
CyberStrong Can Help
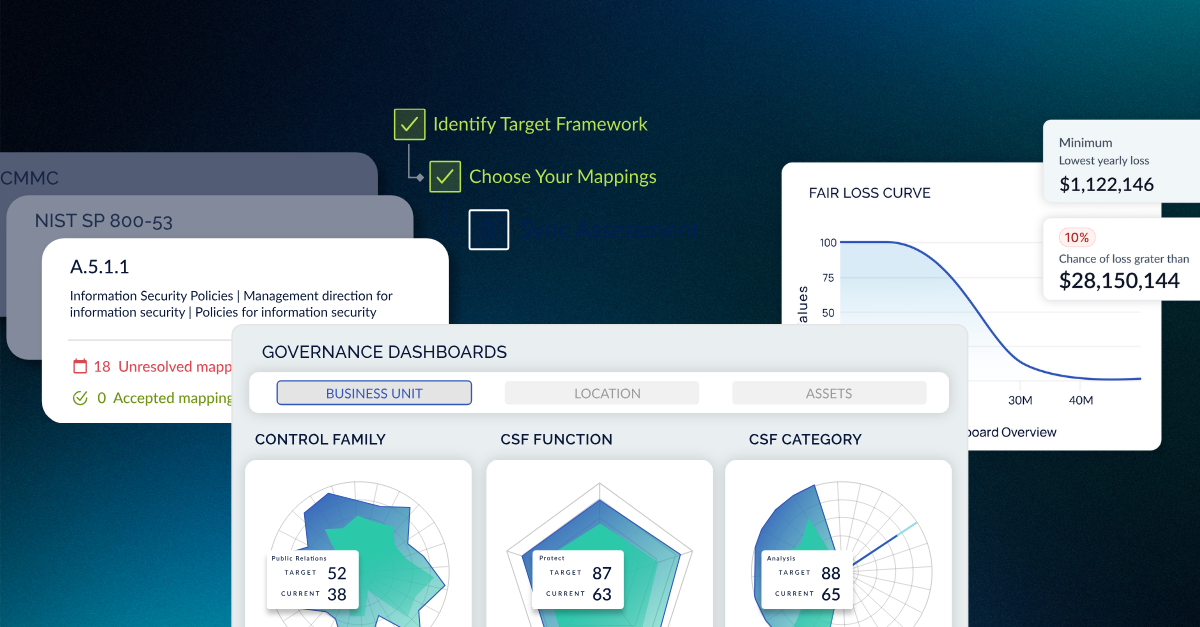
CyberStrong is an all-inclusive platform that offers unparalleled support and visibility into risk, creates resilience, and automates IT compliance.
The Compliance Management capabilities of CyberStrong help you eradicate redundant manual effort, constantly improve your amenability posture, and enables you to stay ahead of regulatory changes. The result? You develop a more efficient process with a collective action plan and increased productivity for a more scalable and vigorous cyber program.
Embrace agility, automation, and flexibility in the digital landscape by leveraging CyberStrong. If you want to explore incident response capabilities, check out these webinars. Contact us to find out how we can be your partners in creating a safer future for your organization.





.png)
.png)
.png)
%201.png)
.png)