The Compliance Landscape
Cybersecurity and cyber-related compliance regulations and legislation were created to make sure that organizations in all industries and sectors effectively implement cybersecurity best practices. Frameworks and standards such as HIPAA, 23 NYCRR 500, PCI-DSS, GDPR, NIST, and others were created to improve the security of the systems and processes related to transactions and other activities in an enterprise that concern sensitive data. Thus, a security assessment is necessary and common... important in showing due diligence, but oftentimes falls victim to resource constraints.
Compliance teams and professionals are critical players in assuring these important requirements are met. These organizations want to minimize any and all risks to the business – if these risks become real vulnerabilities that lead to incidents, the organization’s customer retention, reputation, and ability to recover financially could suffer greatly. Thus, compliance, audit, and security professionals are in the hot seat to deliver the security guidelines for the organization in a way that everyone can understand and adhere to.
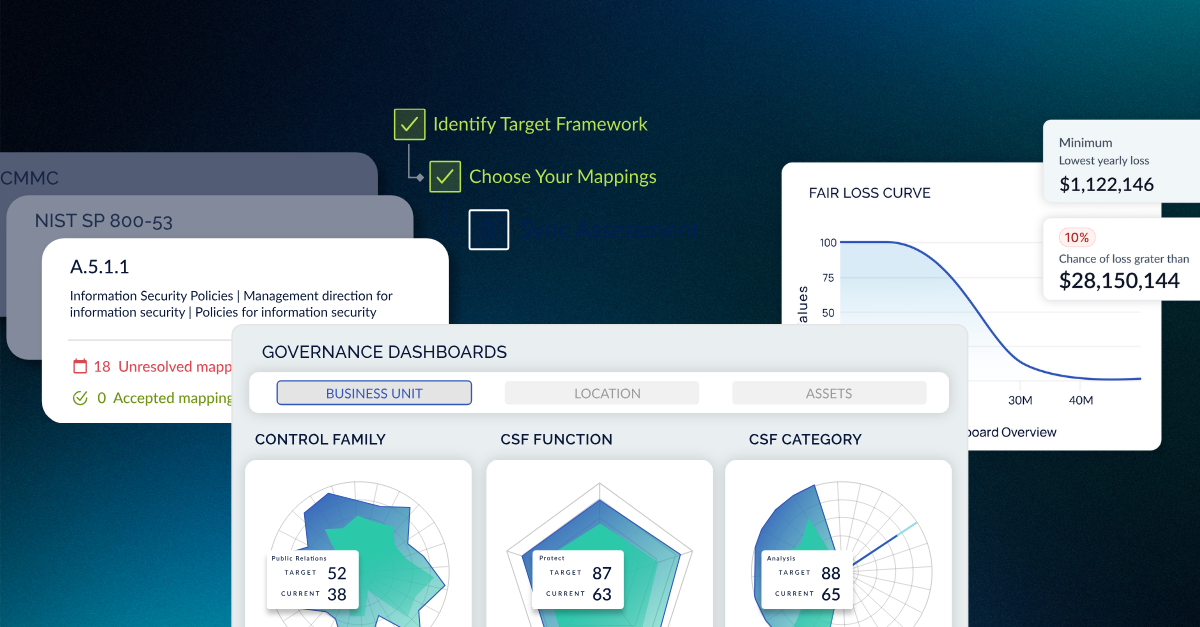
Choosing a framework to assess your organization against is better than having a laundry list of various compliance measures. Why? Because frameworks were created to add depth and breadth to your program in its entirety, and many are specific to how your organization likely operates and interacts with sensitive data. Go beyond a compliance checklist. Use a framework to develop a well-rounded, comprehensive program that is recognized as legitimate and will help you prove due diligence in the future.
Compliance Isn’t ‘Simple’
Meeting compliance, however, is no easy task. Unfortunately, only a subset of the enterprise actually plays a part in making sure that company data is secure through compliance measures—it’s hard to get the non-security teams interested in the goals and objectives of the cybersecurity and InfoSec teams, especially around something as seemingly dry as compliance.
At CyberSaint, we’ve seen organizations where those performing the assessment and gathering the data took weeks chasing their non-security peers around for the information necessary for completion.
Especially in the last five years, technology has evolved, and digitization has taken over. You’d think that cybersecurity best practices would be following suit. No such luck – for organizations to implement best practices, there’s a lot of human effort required along with training and budgeting that’s involved. Cyber risk is growing as more uninformed or poorly-trained employees are to blame for mishandling or using company data in non-compliant ways, which leads to vulnerabilities.
Are You Swinging Spreadsheets or Battling Complexity?
Those who work in compliance know all too well that human effort adds a lot of variables to compliance projects. As an information security professional looking to make your compliance program more efficient, it can be tough to watch your team members wrestle with spreadsheet after spreadsheet for every assessment or audit you are required to complete and report on. Not only that, but the human aspect of data collection as you walk through your assessment makes the timeframe within which it can be completed grow, depending on how fast you can gather information from your team members and non-security peer groups.
Spreadsheets aren’t only not scalable, but they’re not living, breathing accounts of your compliance posture. When using spreadsheets, you need to do the heavy lifting to make the reports you need, and the idea of ‘continuous compliance’ is out of sight. Measurability is difficult if you’re filling in cells as accounts of control requirements and remediation steps. Massive spreadsheets are left open on desktop computers, and one after another, the requirements are assessed, and potential risks are identified.
On the other end of the spectrum, we have complex solutions. These solutions have their place, but for the assessment aspect of GRC (Governance, Risk, and Compliance), they fall short. With more and more automation working its way into technology solutions, you would assume they’d have their fair share of automation as well. Unfortunately, this isn’t the case, and at CyberSaint, we’ve seen large organizations come to us because their heavily configured, hard-to-implement solution just isn’t doing it for them. Quick, agile, automated assessments that allow for continuous compliance and company-wide workflow are what they want, but not what they’ve experienced.
Neither of these methods empowers teams to implement agile and widely-understood assessment processes, continuous compliance, or to truly measure their compliance posture.
It’s Time to Come Out of The Dark Ages.
If you’re working in cyber, risk, or data compliance and governance, you deal with lots of data, and your job requires real intellect. You shouldn’t be wasting that knowledge fumbling with spreadsheets or slow solutions that seem like they were created circa 2006. It’s time to bring agility, simplicity, and tribal knowledge to cyber compliance. The rest of the world around is evolving with digitization and technology – as compliance experts, why can’t our assessment, audit, and reporting processes evolve too?





.png)
.png)
.png)
%201.png)
.png)