Compliance Automation at Enterprise Scale
Automate continuous compliance with Agentic Evidence Collection and Continuous Control Monitoring. Powered by patented AI and used by customers in the Fortune 500, take audit prep to the next level with rapid time to value and scalability.
TRUSTED BY INDUSTRY LEADERS

Real Automation. Delivered.
0 M+
0 %
> 0 %
AI-Powered Compliance Automation
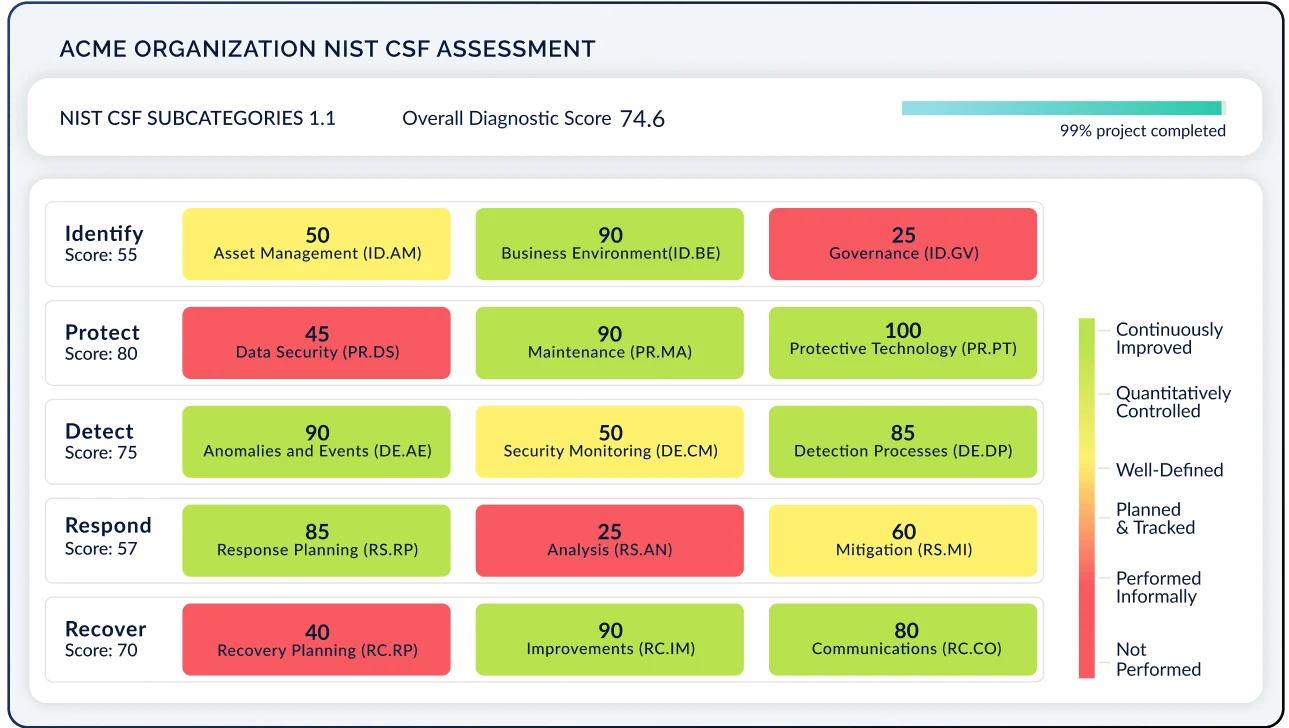
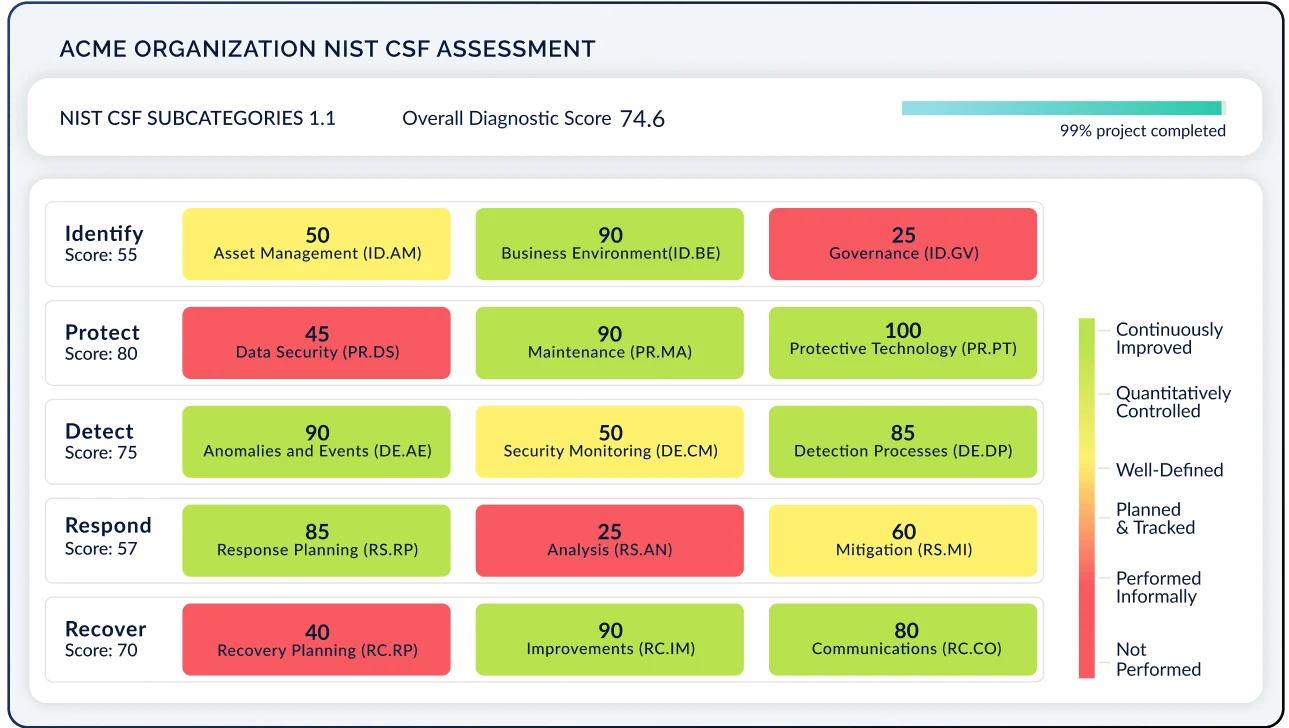
Continuous Control Monitoring and Agentic Evidence Collection take you from a reactive to a proactive assessment approach. Automate control scoring and evidence validation in real-time, and project your results across other frameworks. Gone are the days of manually preparing for audits. Instead, monitor gaps and address them before they are exploited.
What is Continuous Control Monitoring?
Our Continuous Controls Monitoring capability integrates with your security tech stack, understands the data flowing from those various solutions, and maps those live data points onto control frameworks, thereby automatically testing and scoring those controls along any given scoring model. CCM elevates compliance from static to dynamic, scoring controls in real-time as data from your assets change and eliminating time and resource spent on manual assessments.

What is Agentic Evidence Collection?
Agentic Evidence Collection uses autonomous AI agents to continuously gather audit-ready evidence from across your tech stack, without relying solely on APIs. These agents operate within strict security guardrails, ensuring safe, permissioned access while covering environments traditional integrations can’t reach. The result is broader coverage, less manual screenshots to fulfill auditor requests, and real-time assurance that your controls are working as intended.
How Does Compliance Automation Work?
We take a look at your security environment, normalize your security telemetry, and ensure it aligns with the appropriate control framework. Our 1-click API integrations are up and running in seconds, and agents are configured with secure guardrails to collect the evidence that APIs can't. Key data tags such as Asset, Resource Group, and Policy are meticulously organized. CyberSaint's team ensures data is correctly formatted and mapped to the control framework using an NLP engine, with additional expert review.
How Often is My Assessment Updated?
You choose how often your assessment runs. These automation checks can be daily, weekly, monthly or quarterly as needed. Each schedule is unique to each security telemetry source based on a predefined value roadmap, culminating in the comprehensive automation of your control testing at a cadence that works for you. Move beyond point-in-time checks to dynamic, real-time compliance against frameworks, enhancing accuracy and reducing manual effort.
What is Continuous Control Monitoring?
Our Continuous Controls Monitoring capability integrates with your security tech stack, understands the data flowing from those various solutions, and maps those live data points onto control frameworks, thereby automatically testing and scoring those controls along any given scoring model. CCM elevates compliance from static to dynamic, scoring controls in real-time as data from your assets change and eliminating time and resource spent on manual assessments.

What is Agentic Evidence Collection?
Agentic Evidence Collection uses autonomous AI agents to continuously gather audit-ready evidence from across your tech stack, without relying solely on APIs. These agents operate within strict security guardrails, ensuring safe, permissioned access while covering environments traditional integrations can’t reach. The result is broader coverage, less manual screenshots to fulfill auditor requests, and real-time assurance that your controls are working as intended.
How Does Compliance Automation Work?
We take a look at your security environment, normalize your security telemetry, and ensure it aligns with the appropriate control framework. Our 1-click API integrations are up and running in seconds, and agents are configured with secure guardrails to collect the evidence that APIs can't. Key data tags such as Asset, Resource Group, and Policy are meticulously organized. CyberSaint's team ensures data is correctly formatted and mapped to the control framework using an NLP engine, with additional expert review.
How Often is My Assessment Updated?
You choose how often your assessment runs. These automation checks can be daily, weekly, monthly or quarterly as needed. Each schedule is unique to each security telemetry source based on a predefined value roadmap, culminating in the comprehensive automation of your control testing at a cadence that works for you. Move beyond point-in-time checks to dynamic, real-time compliance against frameworks, enhancing accuracy and reducing manual effort.
Built on Patented AI-Powered Automation
Take your cyber risk management program from point-in-time to real-time with proven technology that delivers unquestionable value
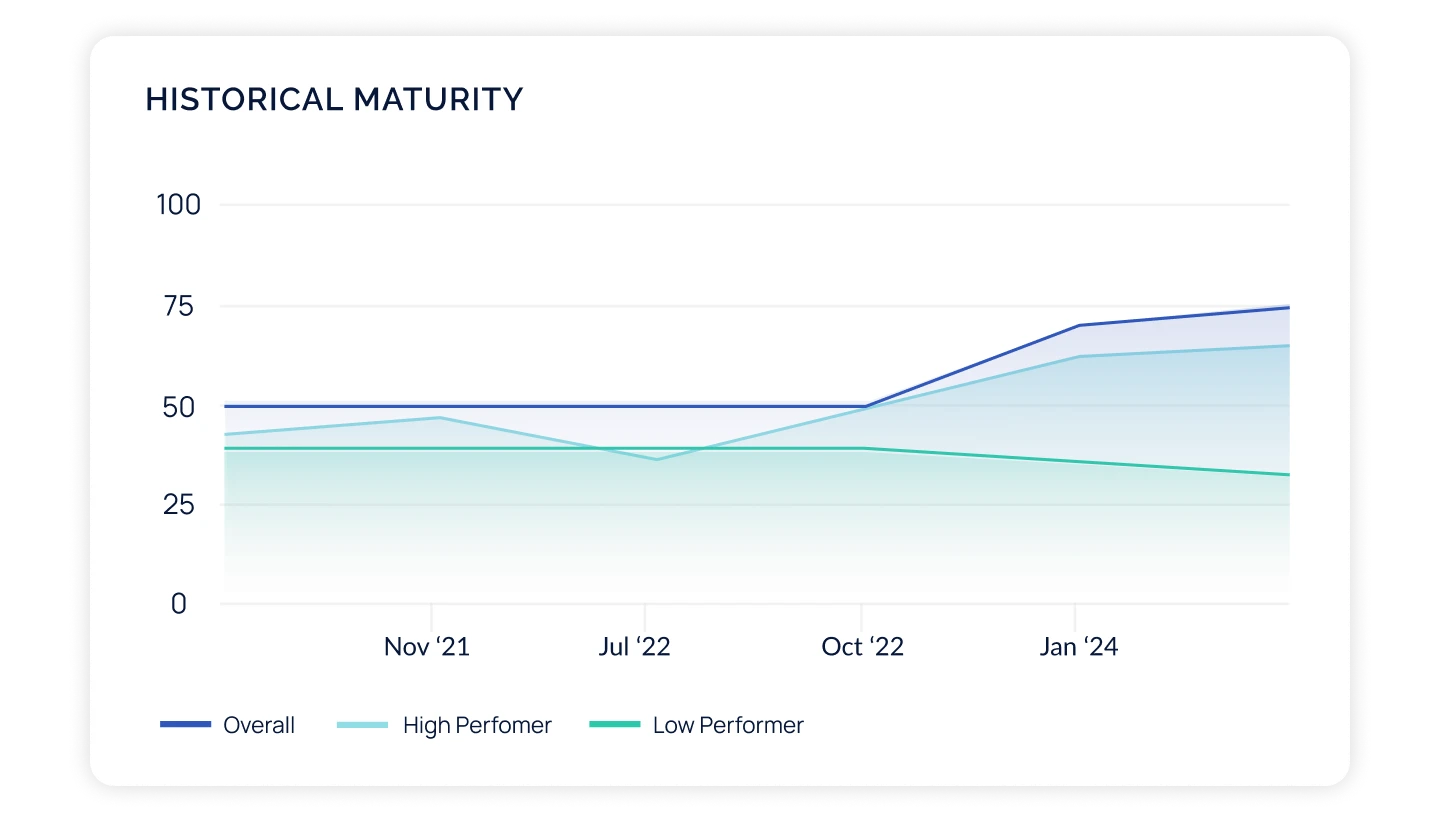
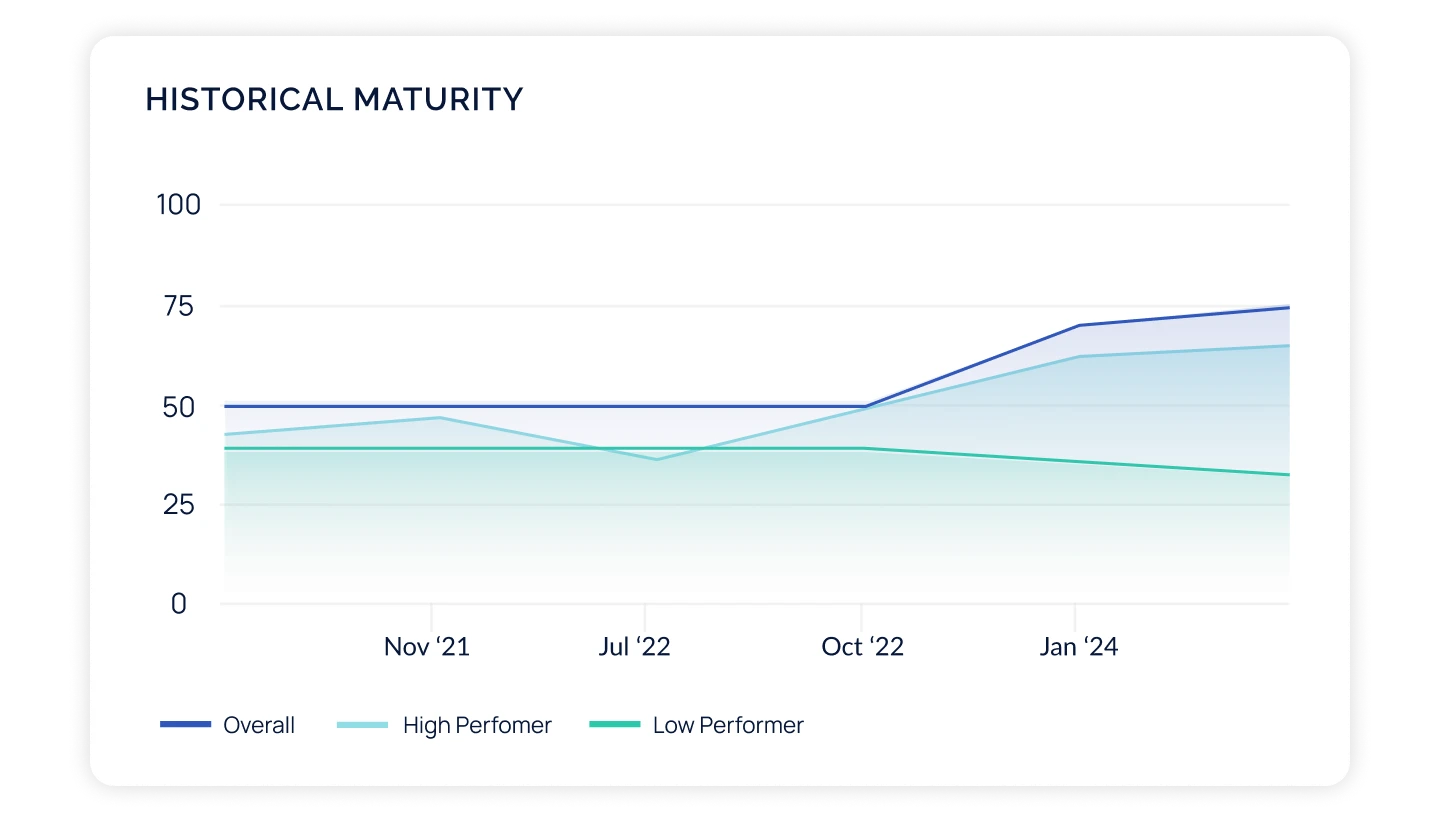
Unlock Increased Value as Your Program Matures
CyberStrong is designed to grow with you. Get instant results by starting with the software package that aligns with your immediate needs and unlock functionality as your strategy evolves.
Compliance Hub
Risk Hub
Executive Hub
Compliance Hub
The most basic CyberStrong package, built to address risk-based compliance management.
- Uncover what top cyber risks impact your business, and use these insights to inform your control assessment strategy
- Access a flexible controls library, hundreds of frameworks, and perform assessments
- Harmonize frameworks with AI-powered automated crosswalking to "assess once, use many"
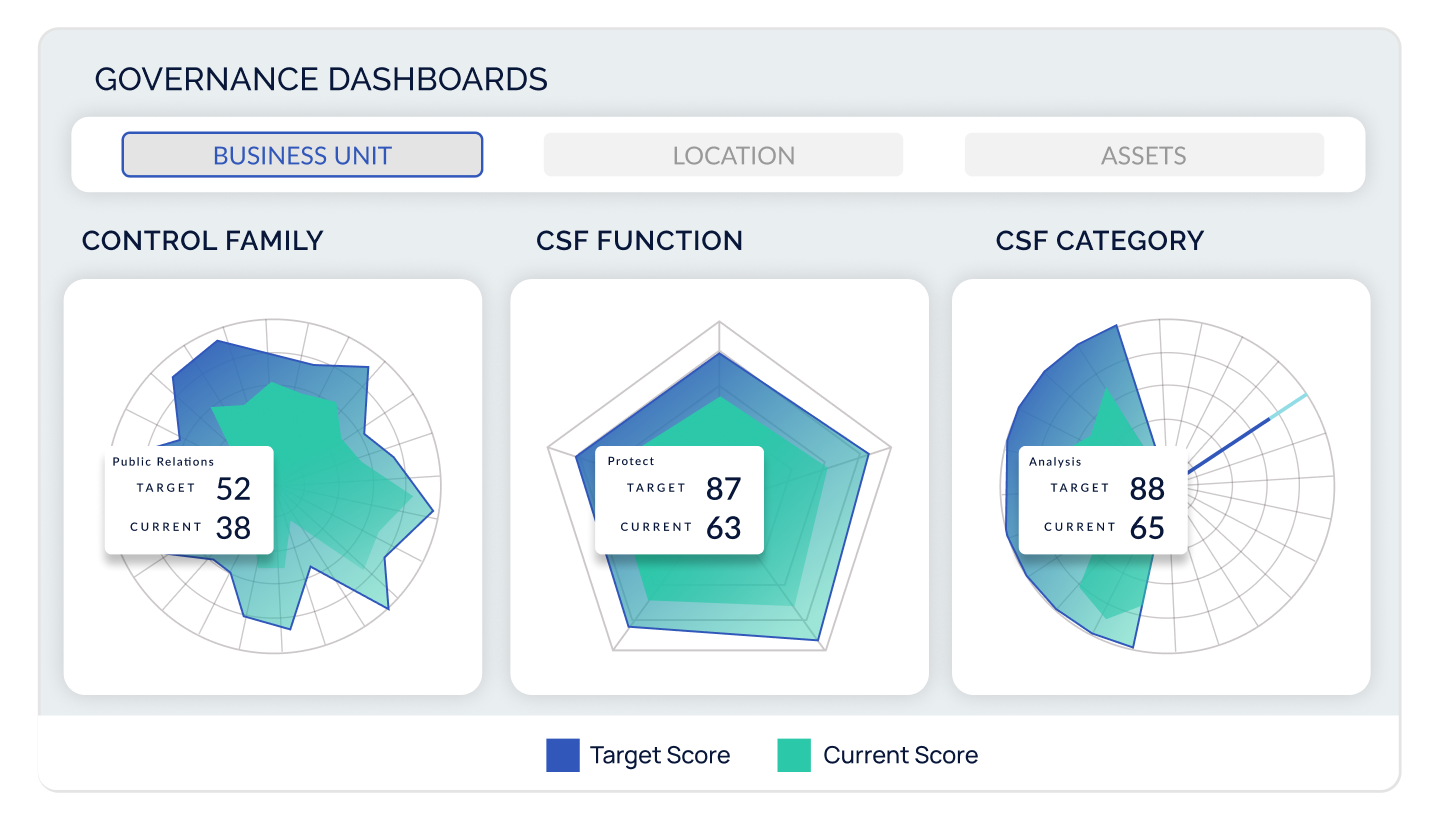
- Leverage flexible dashboards and reports to track trends over time, gap-to-goal analysis, and view compliance by geography, business unit, assets, and more
Risk Hub
Designed to connect the dots between controls, risks, and finance, the Risk Hub includes everything in the Compliance Hub plus the ability to:
- Tie control groups from assessments and frameworks you are already tracking to risks in an intuitive risk register
- Benchmark your top risks versus those of your peers based on industry, company size, and revenue
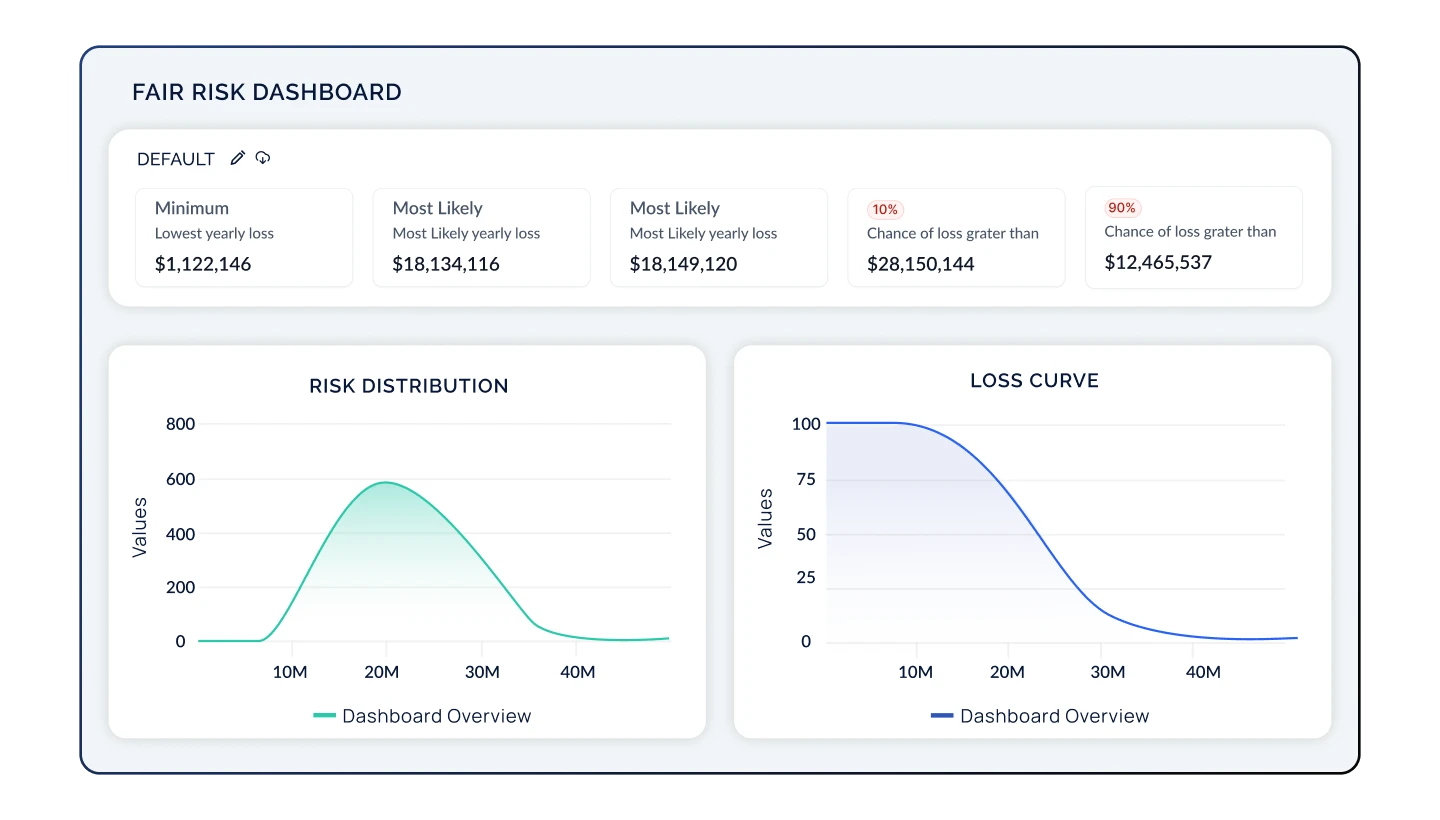
- Quantify risk into financial metrics with transparent models such as FAIR and NIST 800-30, designed for rapid implementation and scalability
- Customize heat maps, risk dashboards, and reports to view risk from any angle

Executive Hub
Our most robust package, the Executive Hub elevates the cyber risk conversation. Leverage everything offered in the Risk Hub, plus the ability to:
- Present cyber risk initiatives in a business context, making complex cyber risk data accessible and understandable to non-technical stakeholders, regulators, and cross-functional teams, especially the C-Suite and Board
- Influence budgeting decisions by modeling out security investments with clear remediation project timelines, tracking, and ROI analysis
- Refine and optimize your cyber risk strategy as new controls or risks are added, uncovering new opportunities for risk remediation, budget unlock, and value creation on an ongoing basis
Becoming CyberStrong
CyberStrong has transformed our approach to cyber risk management. The real-time insights and automated assessments have not only streamlined our processes and saved costs but have also significantly enhanced our decision-making capabilities. I feel confident justifying the dollars in my budget towards key initiatives, because I can quantify the impact we're making.
Thanks to CyberStrong, we can now present our cybersecurity strategy and its financial implications to our executives in a language they understand. This has significantly improved executive buy-in and the maturity of our cyber practice.
The SEC requirements have elevated the conversation around cyber risk to the Boardroom. CyberSaint’s platform not only hits on the need for increased automation at the foundational compliance level, but also the need to link controls to risks to make cyber risk management real-time. Companies now can have a clear understanding of their cyber risk posture and optimize accordingly based on their most likely cyber losses, risk mitigated, and ROSI. Translating cyber risk into financial terms is a game-changer for C-suites and Boards, and CyberSaint has cracked the code on rapid time to value and scalability for enterprise cyber risk quantification. The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.
CyberStrong has transformed our approach to cyber risk management. The real-time insights and automated assessments have not only streamlined our processes and saved costs but have also significantly enhanced our decision-making capabilities. I feel confident justifying the dollars in my budget towards key initiatives, because I can quantify the impact we're making.
Thanks to CyberStrong, we can now present our cybersecurity strategy and its financial implications to our executives in a language they understand. This has significantly improved executive buy-in and the maturity of our cyber practice.
The SEC requirements have elevated the conversation around cyber risk to the Boardroom. CyberSaint’s platform not only hits on the need for increased automation at the foundational compliance level, but also the need to link controls to risks to make cyber risk management real-time. Companies now can have a clear understanding of their cyber risk posture and optimize accordingly based on their most likely cyber losses, risk mitigated, and ROSI. Translating cyber risk into financial terms is a game-changer for C-suites and Boards, and CyberSaint has cracked the code on rapid time to value and scalability for enterprise cyber risk quantification. The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.
RESEARCH SPOTLIGHT
Explore the Gartner® Hype Cycle™ for Cyber-Risk Management, 2025
As the digital world evolves, so does the sophistication of cyber risks and regulatory pressures. Continuous Control Monitoring (CCM) automates the monitoring of cybersecurity controls’ effectiveness and relevant information gathering in near-real time.
Security and risk leaders can improve their organization’s security posture and their own productivity by adopting Continuous Control Monitoring technologies. Learn why CyberSaint is highlighted as a Sample Vendor for CCM for the second consecutive year in the report
CYBERSTRONG PLATFORM DEMO
See CyberStrong in Action
CyberStrong is built on the principles of innovation, simplicity, and effectiveness, empowering you to continuously optimize your cyber posture with data-driven insights. We're excited to meet you!
What to expect:
-
Customer-Centric Discovery: This time is yours. We start by listening to you—understanding your unique challenges and goals. This enables us to propose solutions that can meet the specific needs of your industry and organization.
-
Interactive Platform Walkthrough: Get hands-on experience with our platform, from control automation to cyber risk quantification. See firsthand how CyberStrong turns complex cyber risk and compliance data into action.
-
Expert Guidance: Engage with our experts who will be available to answer your questions, discuss best practices used by our customers, and show you how CyberStrong integrates with your existing security infrastructure to enhance your cyber resilience.
What the community is saying...
The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.





.png)
