MEASURE YOUR RESULTS
CyberStrong
Executive Hub
Present cybersecurity initiatives as strategic business opportunities with a full-cycle cyber risk management solution
CyberStrong Executive Hub
The CyberStrong Executive Hub offers solutions across every facet of the cyber risk management lifecycle and is designed to bridge the gap between cybersecurity risks and business objectives
Showcase the Business Value of Cybersecurity
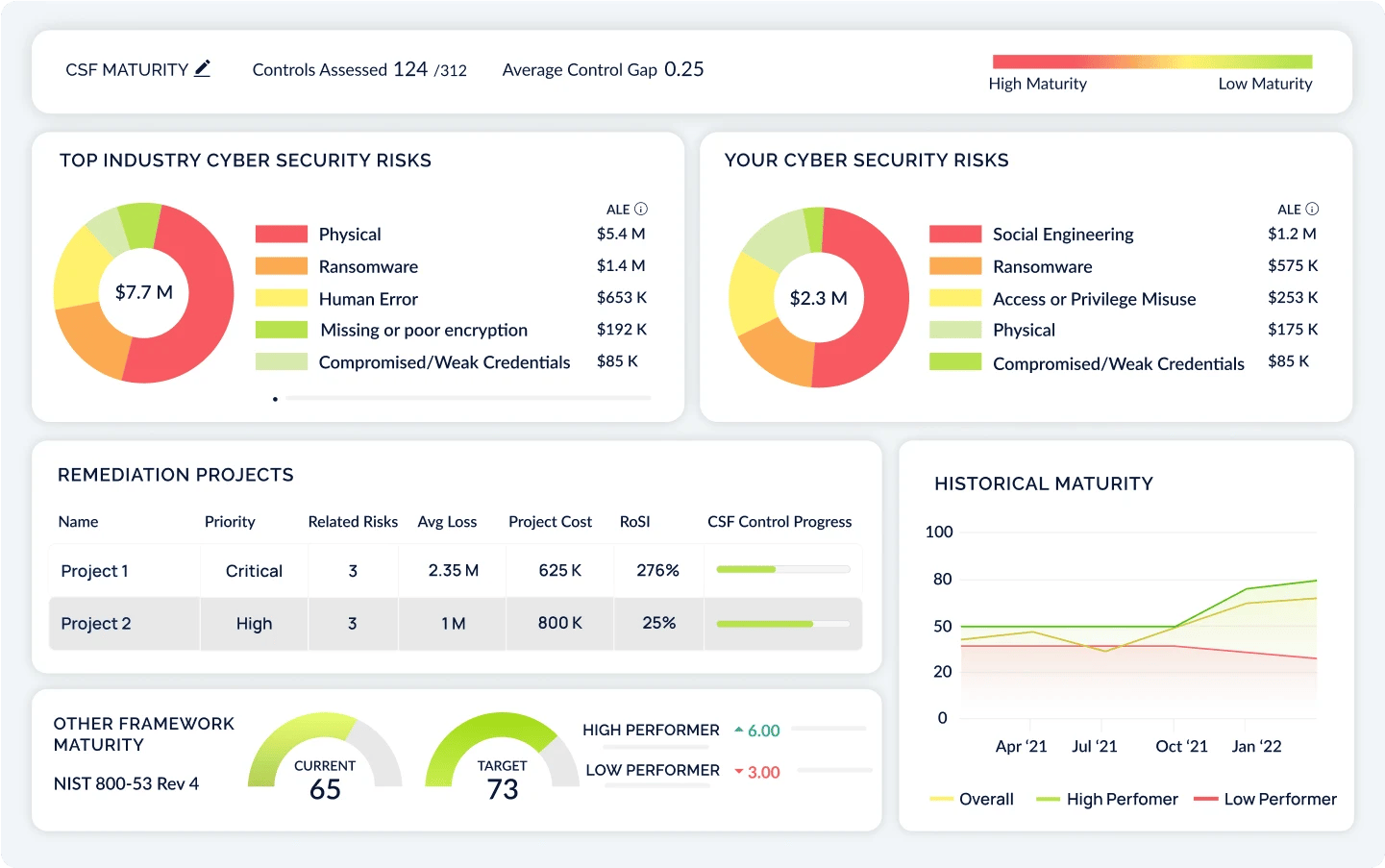
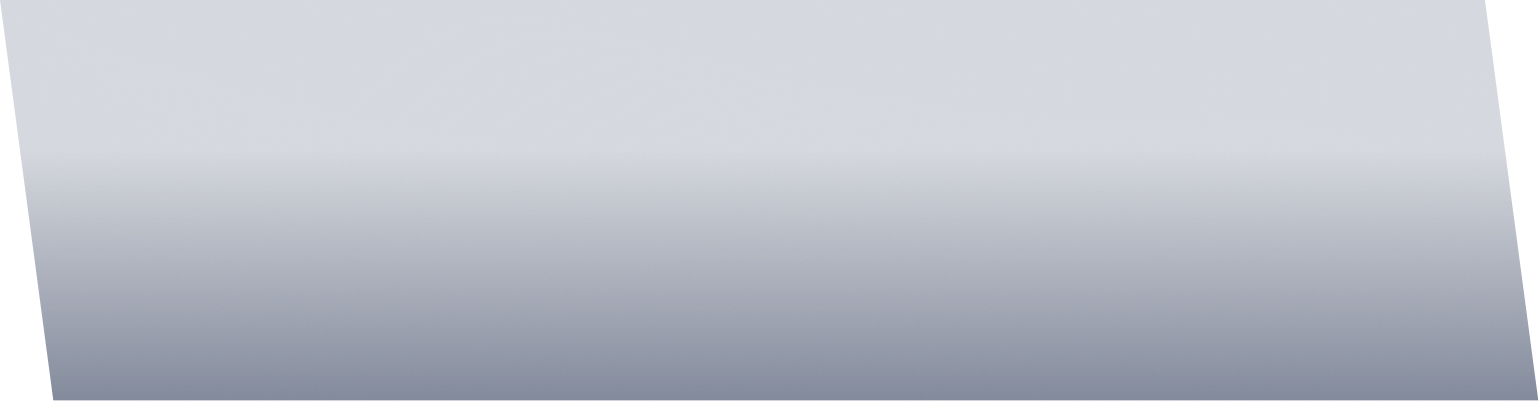
Translate your cyber risk posture into financial terms, aligned to business objectives, that resonate with CFOs, CEOs, or other business leaders.

Facilitate Strategic, Data-Driven Decision-Making
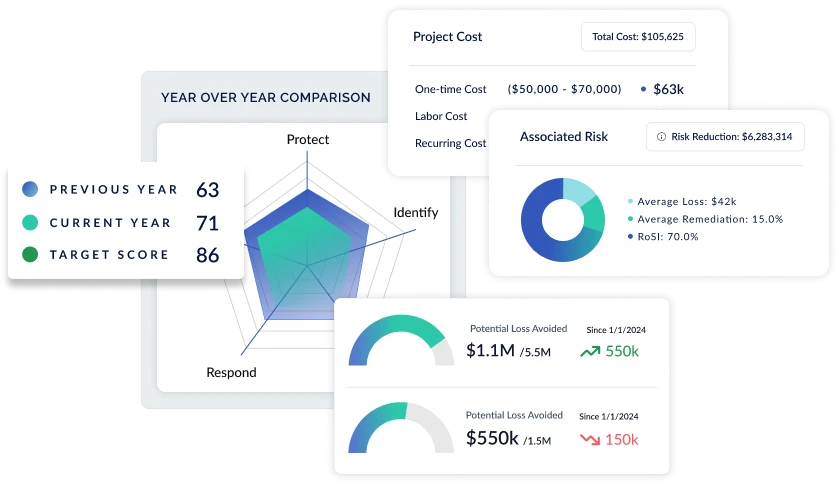
Prioritize actions that align with desired impacts on the bottom line, leveraging a detailed yet clear depiction of risk scenarios, the business impact of risk mitigation, and Return on Security Investment (ROSI).
-1.png)
Track Remediation Progress and Risk Buydown
Monitor remediation projects in real-time and effectively measure the reduction of cyber risks, ensuring strategic alignment with business objectives. Provide a clear and concise view of your cyber risk posture, potential losses, remediation projects, and proposed returns.
Continuously Adapt and Enhance Your Cyber Risk Strategy
Continually update and refine your cyber risk strategy based on dynamic data and analytics, additional control frameworks, and newly uncovered risks. Ensure your organization remains resilient and proactive in reducing your cyber risk exposure as new threats emerge.

CYBER RISK INSIGHTS
A Step-by-Step Playbook for Cybersecurity Board Reporting
Gain the knowledge needed to create a robust reporting framework that communicates your cyber posture, facilitates informed decision-making at the board level, and meets SEC requirements. Learn practical steps and strategies to articulate cybersecurity risks, impacts, and mitigation efforts in a manner that aligns with the SEC's requirements and supports collaboration between the CISO, CFO, CEO, and Board.
Becoming CyberStrong
CyberStrong's industry risk insights have provided us with a clear understanding of our specific risk profile, helping us to tailor our security strategies more effectively. The platform's data-driven approach is truly impressive.
The SEC requirements have elevated the conversation around cyber risk to the Boardroom. CyberSaint’s platform not only hits on the need for increased automation at the foundational compliance level, but also the need to link controls to risks to make cyber risk management real-time. Companies now can have a clear understanding of their cyber risk posture and optimize accordingly based on their most likely cyber losses, risk mitigated, and ROSI. Translating cyber risk into financial terms is a game-changer for C-suites and Boards, and CyberSaint has cracked the code on rapid time to value and scalability for enterprise cyber risk quantification. The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.
With CyberStrong, we've been able to quantify our cyber risks in financial terms, making it easier to prioritize investments in our cyber defenses. The platform's ability to simulate RoSI and project timelines has been invaluable for my business-side discussions.
CyberStrong's industry risk insights have provided us with a clear understanding of our specific risk profile, helping us to tailor our security strategies more effectively. The platform's data-driven approach is truly impressive.
The SEC requirements have elevated the conversation around cyber risk to the Boardroom. CyberSaint’s platform not only hits on the need for increased automation at the foundational compliance level, but also the need to link controls to risks to make cyber risk management real-time. Companies now can have a clear understanding of their cyber risk posture and optimize accordingly based on their most likely cyber losses, risk mitigated, and ROSI. Translating cyber risk into financial terms is a game-changer for C-suites and Boards, and CyberSaint has cracked the code on rapid time to value and scalability for enterprise cyber risk quantification. The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.
With CyberStrong, we've been able to quantify our cyber risks in financial terms, making it easier to prioritize investments in our cyber defenses. The platform's ability to simulate RoSI and project timelines has been invaluable for my business-side discussions.
Unlock More Value From CyberStrong
CyberStrong is designed to grow with you. Start with CyberStrong Compliance or Risk Hub and add on the Executive Hub capabilities when you're ready.
Compliance Hub
The foundational Hub of CyberStrong, leverage the CyberStrong Compliance Hub to identify risks and related controls, perform assessments against frameworks and standards, harmonize regulations with automated crosswalking, and view compliance from any angle.
Learn MoreRisk Hub
Everything in the Compliance Hub, plus a flexible risk register, risk dashboards and reports, and a credible approach to cyber risk quantification. Manage your risk posture and clearly communicate cybersecurity in financial terms.
Learn MoreCompliance in Motion
Incorporate Continuous Control Automation™ into any CyberStrong Hub and replace manual processes with AI-powered, real-time compliance
Continuous Control Automation™
Score controls automatically as data in your security tech stack changes, moving from point-in-time assessment to real-time assessment
Learn MoreFeatured Resources
Discover the essentials of cyber risk management and enhance your expertise

2025 Gartner® Hype Cycle™ for Cyber-Risk Management

AI-Powered Findings Management Solution Brief
Key Takeaways from Gartner's Market Guide for TPRM Technology Solutions
CYBERSTRONG PLATFORM DEMO
See CyberStrong in Action
CyberStrong is built on the principles of innovation, simplicity, and effectiveness, empowering you to continuously optimize your cyber posture with data-driven insights. We're excited to meet you!
What to expect:
-
Customer-Centric Discovery: This time is yours. We start by listening to you—understanding your unique challenges and goals. This enables us to propose solutions that can meet the specific needs of your industry and organization.
-
Interactive Platform Walkthrough: Get hands-on experience with our platform, from control automation to cyber risk quantification. See firsthand how CyberStrong turns complex cyber risk and compliance data into action.
-
Expert Guidance: Engage with our experts who will be available to answer your questions, discuss best practices used by our customers, and show you how CyberStrong integrates with your existing security infrastructure to enhance your cyber resilience.
What the community is saying...
The CyberStrong platform is a powerful solution for every enterprise CISO looking to master their cyber risk posture.






.png)
