In his predictions for 2019, Deloitte CEO of Risk and Financial Advisory, Chuck Saia, emphasized the necessity for compliance and risk professionals to involve business leaders -
"To engage senior leaders, the CIO and CISO should develop business-focused cyber risk reporting, rather than overly technical reports with a focus on business impacts and risks,"
Chuck Saia, Deloitte CEO of Risk and Financial Advisory
Saia noted that today only 30% of CEOs and board members were highly involved in their organization's security programs. However, by 2020, 100% of large enterprises will be asked to report to their board of directors on cybersecurity and technology risk at least annually, which is an increase from today's 40%. (Gartner).
With cybersecurity rapidly becoming a board-level issue, many CISOs face the same level of inquiry and scrutiny as a CFO or CEO. Cyber is no longer an abstract concept that can be assessed with the question ‘Are we secure?’ and a brief ‘Yes’. According to Gartner, successful CISOs are leaders, communicators, and managers. All CISOs need to be prepared to convey their organization's progress to ensure the enterprise stays secure as it continues to grow.
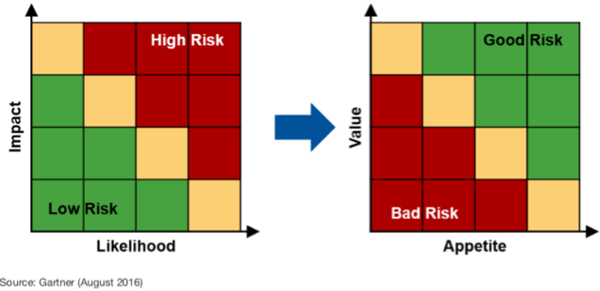
Shifting the conversation from high/low risk to good/bad risk
The issue many CISOs
Effective CEOs are trained to take the right business risks to drive growth. In order to get buy-in from their CEO, a CISO must reframe the inherent risks of new initiatives from a high/low model to a good/bad risk model. This shift requires a CISO to align their activities with business goals - instead of assessing risk through the lens of likelihood and impact, the good/bad risk framework looks at it through the lens of value and appetite.
71% of non-IT executives said that concerns over cybersecurity are impeding innovation in their organizations - Gartner
Don’t be seen as an impediment to business progress - by aligning cybersecurity activities with business goals and taking a good/bad risk approach. You can effectively communicate the impact of new initiatives and help non-IT executives understand the inherent risks.
The 4 Reports To Effectively Communicate With Key Stakeholders
As enterprise stakeholders take an increasing interest and concern about the security posture, the CISO needs to be able to convey their activities and success as effectively as a CFO can with a balance sheet and statement of cash flows. Four recommended reports are necessary to help you align your activities as a CISO with the goals and objectives of the enterprise: Executive Risk Report, Trend Report, GDPR Report, and Global Report.
Executive Risk Report
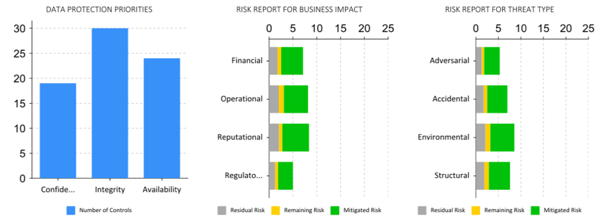
An Executive Risk Report delivers a high-level overview of the company’s risk. The report has three critical breakdowns: risk by threat type, risk by business impact, and the data protection triad (confidentiality, integrity, availability).
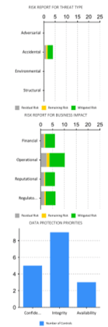
Within the risk by threat type and risk by the business impact, each bar chart reflects the volume of residual risk, remaining risk, and mitigated risk.
The data protection triad reflects the number of controls implemented to protect each dimension. With emerging integrated risk management (IRM) systems like the CyberStrong platform, CISOs are able to see each dimension in the order of priority based on the number of controls employed for each. Within the risk by threat type and risk by the business impact, each bar chart reflects the volume of residual risk, remaining risk, and mitigated risk.
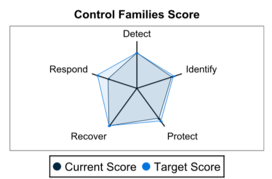
A CyberStrong Executive Risk Report also delivers a risk report breakdown for control families. As CyberStrong is built on the NIST frameworks, this chart is delivered through the lens of NIST’s 800-30 breaking controls into detect, identify, protect, recover, and respond. This chart also reflects the amounts of residual risk, remaining risk, and mitigated risk.
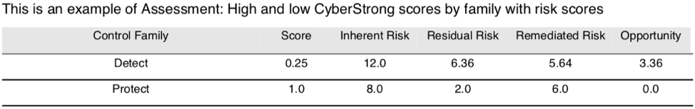
Finally, a CyberStrong Executive Risk report includes a more granular breakdown of the risk posture by the control family. Each family is assigned a CyberStrong score which impacts the risk scoring itself. Unlike the charts above, this table breaks the categories of risk down further: inherent risk (total risk by family), residual risk (the
| Control Family | NIST Classifier | Score | Inherent Risk | Residual Risk | Remediated Risk | Opportunity |
| Detect | D | 63.0 | 13.5 | 5.06 | 8.44 | 1.69 |
| Identify | I | 63.0 | 8.0 | 3.14 | 4.86 | 1.14 |
| Protect | P | 75.0 | 8.0 | 2.5 | 5.5 | 0.5 |
| Recover | R | 67.0 | 5.33 | 2.04 | 3.29 | 0.71 |
| Respond | R | 85.0 | 6.8 | 1.97 | 4.83 | 0.27 |
Trend Report
The CyberStrong Trend Report uses CyberSaint’s patented technology to deliver a CyberStrong score - a rollup of all assessments in the environment and the number of active assessments ongoing. Further, the Trend Report shows the number of assessments and controls updated and several users logged in in the last week. This report will help you display the ongoing progress your organization is making to keep the enterprise secure and is a perfect jumping-off point to discuss more granular activities with non-technical stakeholders.
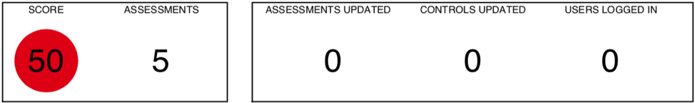
The CyberStrong Trend Report also includes ore granular tables to show the strongest and weakest points in each active assessment. As with the granular table in the Executive Risk Report, these tables use the CyberStrong score combined with a breakdown of inherent risk, residual risk, remediate risk, and opportunity. These breakdowns will help reveal weak points in specific control families and help you and fellow senior leadership prioritize remediation.
The CyberStrong Trend Report also delivers overviews of progress on assessments and updates made to controls in one-month, three-month, six-month, and twelve-month time periods. The Trend Report is your month-over-month and year-over-year progress statement and helps you relay your organization's operations to the Board and CEO.
GDPR Report
General Data Protection Regulation (GDPR) has been a Board level of concern since its enactment in May 2018. As seen with Facebook, the first major infringement, in September 2018, GDPR is a critical concern from both a security and business standpoint. The CyberStrong GDPR Report uses CyberSaint’s list of controls and actions to ensure compliance and increase visibility into GDPR posture on an ongoing basis.
 Reflected in a radar graph comparing the enterprise's posture against the GDPR standard, CISOs and stakeholders get fast insight into their compliance.
Reflected in a radar graph comparing the enterprise's posture against the GDPR standard, CISOs and stakeholders get fast insight into their compliance.
The radar graph is followed by a granular table as seen in the Trend and Executive Risk Reports. This table delivers a deeper view of each control family, matched with a CyberStrong score and breakdowns of inherent risk, residual risk, remediated risk, and opportunity.
The CyberStrong GDPR Report also delivers completed and comprehensive breakdowns of each control necessary for GDPR compliance.
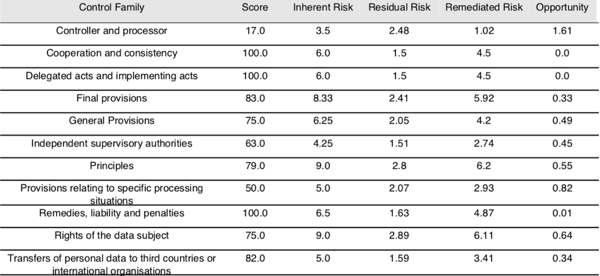
GDPR marked the first legislative correlation between cybersecurity and business operations - and was a very public call to align business and security strategies. The CyberStrong GDPR Report allows CISOs to easily deliver an in-depth review of their enterprise’s GDPR posture to key organizational stakeholders.
Overview Report
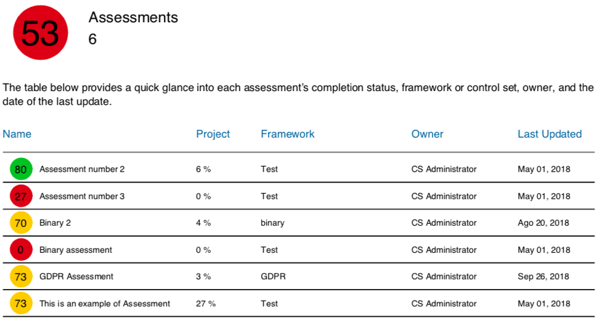
A complete Overview Summary is the fourth critical report necessary to reflect a CISO’s alignment with business strategy. A CyberStrong Overview Summary provides a complete report on an enterprise’s entire assessment environment
The overview highlights the CyberStrong score (using CyberStrong’s risk model). The first is a roll-up score of all ongoing ongoing active assessments. The following table delivers a brief overview of each ongoing assessment, their progress to date, the CyberStrong score, the owner, and when it was last updated. This table is critical for CISOs delivering information on ongoing progress to the CEO and stakeholders.
Similar to the Executive Risk Report, the Overview Summary also delivers bar chart breakdowns of risk report for business impact, risk report for threat type, and data protection priorities for the data protection triad.
 The Overview Summary also delivers a CyberStrong score, a framework description, and a
The Overview Summary also delivers a CyberStrong score, a framework description, and a
The Overview Summary, the most comprehensive report necessary for CISOs, gives stakeholders a deep view of the enterprise's security posture. It helps illustrate the alignment of new business initiatives and the risks that arise as a result.
Be prepared
Cybersecurity increasingly becoming a Board-level matter; CISOs need the ability to report on their progress and activities as efficiently as a CFO can with a balance sheet and statement of cash flows. The four compliance and risk documents (Executive Risk Report, Trend Report, GDPR Report, and Overview Summary) do just that - these reports empower a CISO to effectively communicate their operations to the CEO and Board. With a shift from a high/low to good/bad risk mindset, CISOs present themselves as what they always were - an asset to business operations.





.png)
.png)
.png)
%201.png)
.png)