With an increasing interest in cyber as a business function, security teams and non-technical leaders must be informed of the progress of both business and security. This will enable both sides to be equally informed and ensure the alignment of objectives. Data visualizations that depict the impact of cyber on business are in demand for enterprise leaders to understand the security posture and cyber goals. Cybersecurity dashboards aggregate and consolidate data into functional, presentable, and easy-to-understand images that visualize cybersecurity posture in real-time.
When CISOs present to the board, they must have security and risk information on demand to share with the board. CyberStrong’s Governance Dashboards centralize information automatically and in real time. Security leaders can often fall into the trap of technical jargon and lose the board's interest. Governance dashboards distill the most critical data that displays the impact of investment on the security program and where progress can be made.
GRC platforms and other legacy tools are inadequate solutions built on disparate and siloed processes, employ dated data, and lack a centralized risk data repository. Governance dashboards enable a seamless flow of information up and down the chain of command: view compliance posture by business unit, geography, site, vertical, or any other tagging taxonomy in addition to year-over-year comparisons. Governance Dashboards also utilize the gold standard NIST CSF to inform security posture.
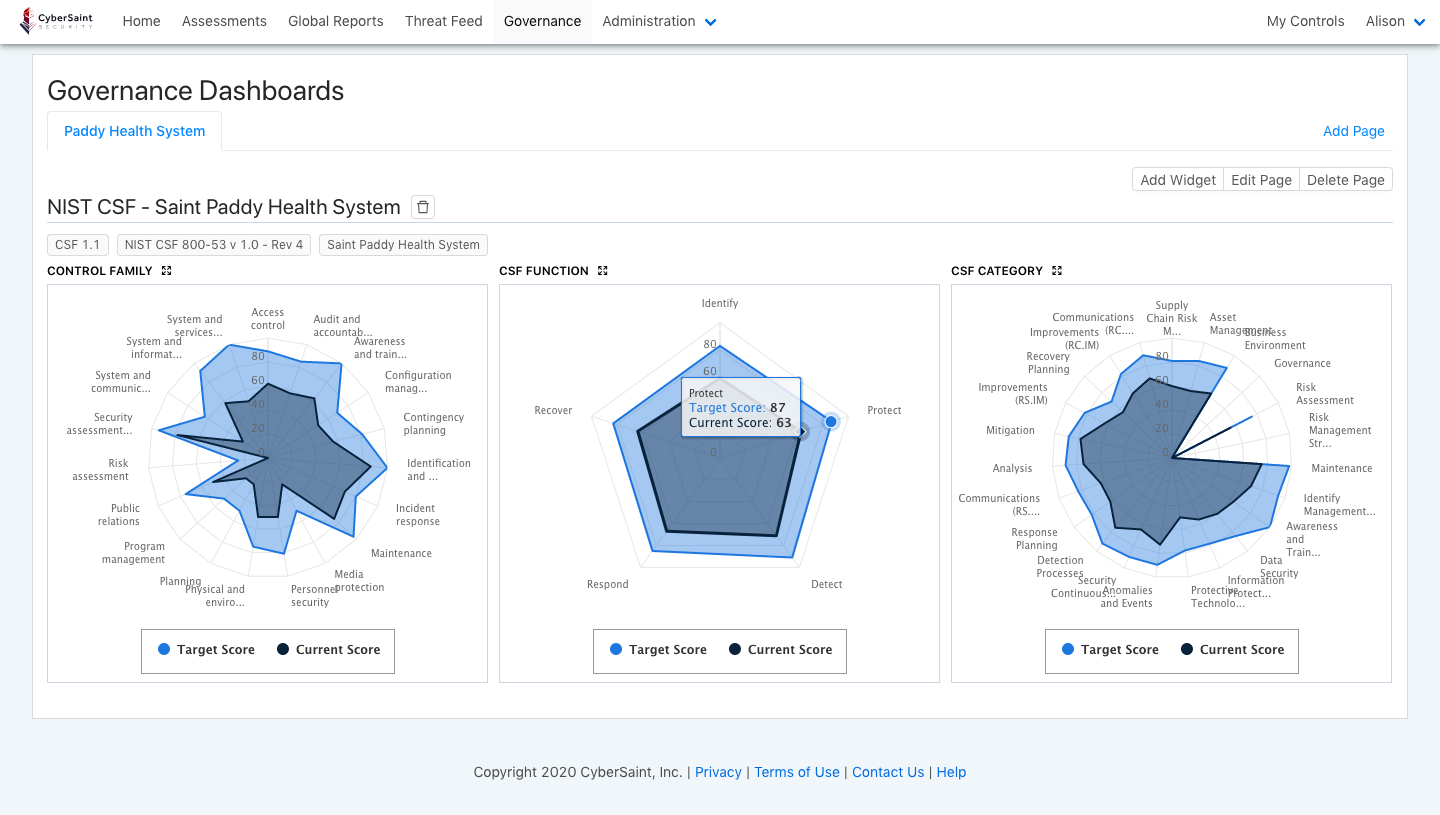
CyberStrong’s Governance Dashboards are meaningful to enterprise-wide governance. Any executive, even with little technical knowledge, will be able to see gaps that require addressing with the security program. These dashboards can enhance the conversation around advancing the cybersecurity program by informing non-technical leaders where gaps exist and validating security investment. This tool shows rather than tells the security posture in easy-to-understand visualizations.
In short, CyberStrong’s Governance Dashboards are ideal for helping CISOs present to the board. They provide real-time information and enable a seamless flow of information up and down the chain of command. Combined with CyberStrong’s Executive Dashboard and CyberStrong’s Assessment Dashboard, visualizing security posture is at your fingertips. Contact us to learn more about how CyberStrong's advanced dashboard function can help you.





.png)
.png)
.png)
%201.png)
.png)