Risk quantification has bridged the security world to the business world. By quantifying risk, security leaders have been able to frame cybersecurity in a business context and illustrate the impact cyber and business have on each other.
With the FAIR (Factor Analysis of Information Risk) model, cyber risk can be broken down into different factors and assigned a monetary value - giving business units greater insight into existing gaps and the impact of time and money on security investments. Using two main categories, loss event frequency and magnitude, cyber and IT teams can determine the risk of cyber threats and potential financial loss.
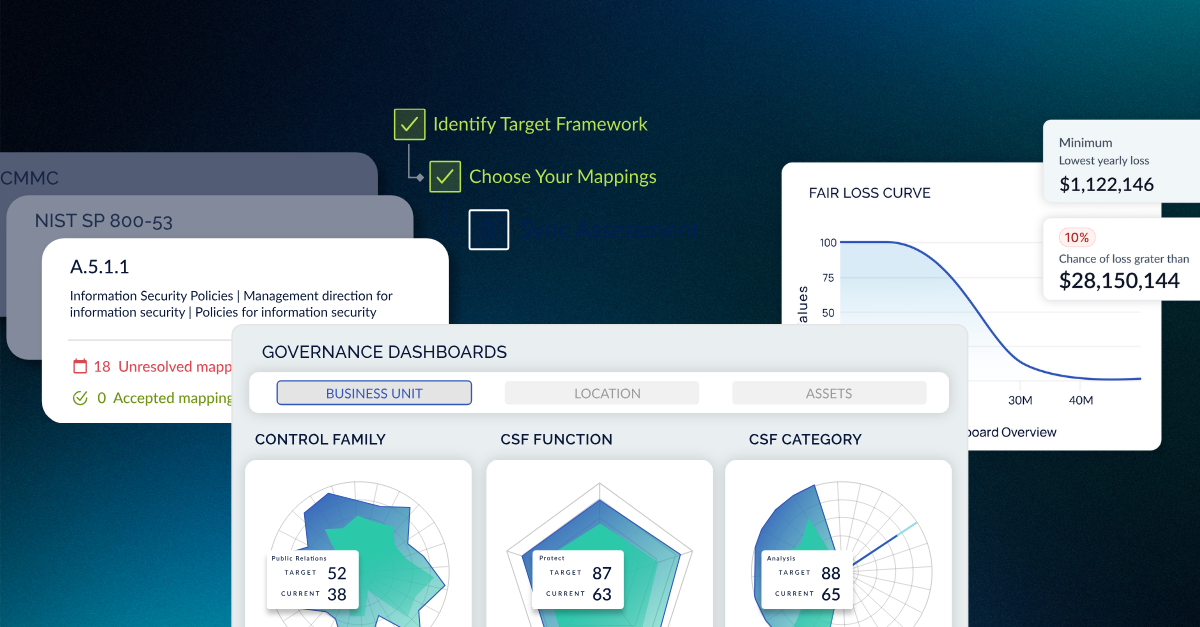
It’s nearly impossible to approach cyber risk quantification with a one-size-fits-all approach. As companies develop their own organizational structures, security programs, and information security management, CyberSaint has incorporated customizable features with the addition of the FAIR model and new updates to its cyber benchmarking functionalities.
A risk register for cybersecurity teams can act as a repository for tracking and identifying cybersecurity risks and is a centralized inventory for business units to refer to. Building from the baseline FAIR model, security teams can incorporate additional mitigation workflows to improve security measures and monitor security posture. To learn more about these new cyber and IT functionalities, watch our webinar Enabling Risk Register Benchmarking with CyberStrong.
CyberStrong’s FAIR Functionality
The CyberStrong platform offers FAIR risk assessment based on the NIST model in addition to adversarial and non-adversarial risk. For effective cyber risk assessment and identification, security teams can use quantitative methods for more accurate risk analysis and glean insights for greater compliance security and risk treatment.
At the top level, users can access loss magnitude and frequency data. As the FAIR functionality is used, additional drill-downs will be available. Users can create a risk distribution chart and a loss exceedance curve based on the FAIR approach and Monte Carlo simulations by entering the minimum, maximum, and most likely values of loss magnitude and frequency. These charts are updated in real-time as the entered values change according to risk assessments.
Users do not have to use separate spreadsheets for Monte Carlo simulations, ensuring greater consistency with calculations. Monte Carlo functionalities are built into the CyberStrong platform, providing users with ease of use and viewing.
Associating Controls Types
Users can begin to build upon this quantified information by associating controls. Like the NIST functionality, security teams can add control groups, a set of controls that may help mitigate a particular risk, like ransomware. The first associated control group will be a baseline for the quantified risk. As the enterprise incorporates more controls and control scores, security teams will gain insight into the progress made and how the estimated risk for ransomware changes.
“Everybody's used to seeing a heatmap red, yellow, green, but now what we're doing is actually letting you visualize it and being able to communicate up to the board and up to the C-levels,” explained Delfin. Moving on from spreadsheets and heatmaps, these new additions include easy-to-understand risk visualizations that help security teams discern where money is being saved or lost and develop financially informed security and risk strategies.
To create a baseline FAIR functionality, three control types must be associated with the control group - protect, detect, and respond. As each control type is added to a group, users can estimate the impact each control group will have on a particular risk related to ransomware. The loss magnitude and frequency functions will continue to update as control groups are updated, giving security teams greater insight into the financial impact of security.
A control type like response will help security teams assess how prepared an organization is to respond to a malware incident. This control type will assess the associated risks and likelihood of a breach based on how fast the malware can be removed and other response measures. Cybersecurity management plans must protect the enterprise’s entire network, not just against ransomware.
Additional Controls
“A big thing to think about with protect, detect, and respond is, if protect was 100% effective, you wouldn't need any other controls, right,” said Scott Shidlovsky, Head of Engineering at CyberSaint.
“Like if nobody is ever going to be able to get through your protection controls and get ransomware on your system, then there's no reason for you to detect it or respond.”
The three main control types cannot function alone. Additional controls like incident response training or phishing security awareness training will have to be incorporated for a stronger mitigation workflow. These additional controls and Monte Carlo simulations will help security teams visualize what the organization can do during a security event. Users will see an updated loss exceedance curve and risk distribution chart with each action and control and develop a baseline set of controls regarding that particular risk.
Enhanced Risk Register Benchmarking
Associating controls to a particular risk is the first step to baselining the FAIR functionality. Utilizing the FAIR methodology and a maintained risk register will create a transparent view of risk and cyber security. With quantified visualizations, CISOs and security leaders can impactfully report cybersecurity to the boardroom with accurate insights and informed methods of action in a crisis
Contact us to see how CyberStrong can be a risk-registering tool for you.





.png)
.png)
.png)
%201.png)
.png)