Factor Analysis of Information Risk (FAIR) is a cyber risk quantification model founded to help businesses evaluate information risks. The FAIR model is maintained as an international standard by the Open Group, a global consortium for technology standards. FAIR is the only international standard quantitative model framework that offers operational risk and information security. This methodology dramatically benefits mature organizations that use cyber risk management solutions.
The primary objective of FAIR is to support the organization’s existing frameworks and risk management strategies. The FAIR risk ontology provides a structured, quantitative approach to understanding information and operational risks. Business executives and board members increasingly rely on FAIR to quantify organizational loss exposure in financial terms for strategic decision-making.
Introduction to Factor Analysis
Factor analysis is a powerful statistical technique used to uncover the underlying factors that drive relationships among various variables. In the realm of information risk management, factor analysis helps organizations break down complex risk factors to better understand how they contribute to risk exposure. The Factor Analysis of Information Risk (FAIR) framework applies this analytical approach to information risk, enabling organizations to identify, quantify, and prioritize the risk factors that matter most. By leveraging factor analysis, the FAIR framework empowers organizations to develop targeted risk management strategies, make informed decisions, and strengthen their overall approach to information risk management.
This analysis of information risk is essential for organizations seeking to proactively address vulnerabilities and align their risk management efforts with business objectives.
Understanding Cyber Risks
Cyber risks represent a significant category of information risk, due to the increasing dependence on digital technologies and interconnected systems. These risks include hacking, malware, ransomware, denial-of-service attacks, and vulnerabilities in software, hardware, and network infrastructure. The consequences of cyber risks can be severe, ranging from financial losses and operational disruptions to reputational damage and regulatory penalties. The FAIR framework provides organizations with a structured methodology for identifying, assessing, and quantifying cyber risks by modeling threat scenarios and estimating their likelihood and impact. By applying the FAIR framework, organizations gain a clearer understanding of their cyber risk landscape and can prioritize their efforts to protect critical assets and ensure business continuity.
FAIR vs. Legacy Risk Quantification Methods
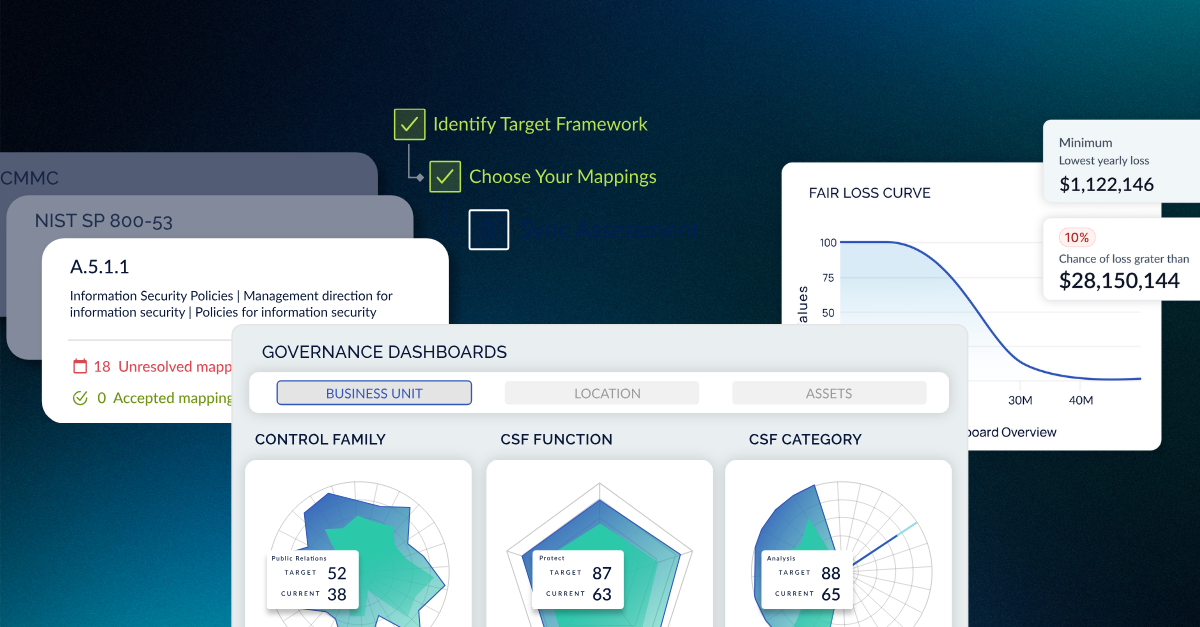
To see how FAIR distinguishes itself from other frameworks, we must understand that FAIR is not a cybersecurity framework like the NIST CSF. It cannot be used as a framework, but is a complementary methodology that works alongside frameworks like NIST, ISO 2700x, and other industry-standard frameworks. FAIR also complements other risk assessment frameworks, such as ISO/IEC 27002, ITIL, OCTAVE, COBIT, and COSO, by providing a scientific and quantitative approach to risk analysis.
Over time, organizations develop compliance gaps, and standard frameworks cannot predict the associated risks. The FAIR methodology identifies an organization’s risks, helps businesses efficiently utilize their resources to create decision-related risk gaps, and scales the threat levels, a feature most frameworks lack. Unlike some risk assessment frameworks that use numerical weighted scales to quantify risk, FAIR emphasizes a scientific and scenario-based approach to risk measurement. Before switching to a risk-based approach, organizations need to decide where they fall on the maturity scale and what GRC solution they will use.
As companies shift from a compliance-based approach to a risk-based approach, they need a risk quantification methodology to support it. FAIR supports this shift in practices, but also helps foster cyber interest among board members and non-technical leaders. The FAIR methodology is unique in that it translates an organization's loss exposure in financial terms, enabling improved communication between technical teams, non-technical members, and leadership.
Unlike the FAIR model, legacy risk quantification models work on penetration testing without internal knowledge of the target system. The testers are unaware of the code and designs that are not publicly available.
Testers can identify the system’s risks and vulnerabilities through this testing, but black-box testing cannot assess the financial impact of those risks. Moreover, with limited knowledge, the test cannot identify all threats and vulnerabilities across organizational models.
Compared to legacy methods or black-box testing, FAIR is a “glass-box,” transparent quantification method that provides leaders with insights into how the metrics were reached. FAIR helps organizations quantify risk by analyzing loss event frequency and loss magnitude, offering a quantitative understanding of risk levels. This allows CISOs to drill down further when presenting to board leaders and executive stakeholders.
The FAIR framework is imperfect despite the vast benefits, extensive security coverage, and excellent threat level identification. Some common drawbacks are:
-
FAIR is comparatively difficult to use because it lacks specific, well-defined documentation of its methods.
-
FAIR cannot independently assess risks. It is a complementary methodology that improves risk assessment by coordinating with other frameworks. Note that FAIR is often used in conjunction with other risk assessment frameworks to provide a more comprehensive view.
-
FAIR relies mainly on probability. Although these probabilities are not baseless, they are not entirely accurate because of the different nature of cyber-attacks and their damage.
The Role of the Fair Institute
The FAIR Institute plays a pivotal role in advancing information risk management by promoting the adoption and effective use of the FAIR framework. By providing resources, thought leadership, and a platform for professional networking, the FAIR Institute supports organizations in building robust information risk management programs and staying ahead of emerging threats. Its commitment to advancing the FAIR framework helps organizations worldwide improve their risk management capabilities and make more informed, data-driven decisions.
The Importance of the External Environment
An organization’s risk exposure is shaped not only by internal factors, but also by the external environment in which it operates. External factors such as regulatory changes, industry trends, technological advancements, and economic conditions can all influence the nature and magnitude of information risk. The FAIR framework recognizes the importance of these external factors and incorporates them into its structured risk analysis approach. By systematically evaluating the external environment's risks and opportunities, organizations can develop more resilient risk management strategies. This holistic perspective enables organizations to anticipate changes, adapt to new challenges, and ensure that their risk management efforts remain aligned with both regulatory requirements and business objectives.
Preparing for a FAIR Risk Assessment
To prepare for a FAIR risk assessment, organizations must start by identifying their cyber network security framework and understanding its complexity and metrics. It is also essential to understand cybersecurity risks and the various threats organizations face, as these can impact decision-making and security posture. Moreover, it is crucial to identify all third-party access to any asset or data.
Before a FAIR risk assessment, you must know the different types of risks. Different risks have different associated outcomes and consequences. For example, sensitive data is a critical asset that attackers could target, making its protection a key consideration. You should be aware of the following risks while using this framework.
-
Compliance risks
-
Operational risks
-
Reputational risks
-
Strategic risks
-
Transactional risks
Once you understand the potential risks that can make your organization vulnerable, you should also identify threat agents who may target sensitive data or exploit vulnerabilities. With this information, you can start the FAIR risk assessment to develop strategies to reduce and resolve the challenges.
Leverage industry best practices and a detailed explanation of the FAIR Model here.
Steps to Take for FAIR Assessment
Use the approach outlined below to successfully implement the FAIR assessment to reduce the risk of breaches and penalties. The FAIR assessment enables organizations to evaluate complex and probable risk scenarios using a scenario modeling construct, helping translate intricate cybersecurity threats and their potential impact into financial terms for better decision-making.
-
Organize your system (system identification, data, vendors, suppliers, accesses, data flow, any 3rd party access, or other factors depending on the company)
-
Identify potential threats (data backup, exposed or breached data, unauthorized access, data exposure, and others)
-
Organize risks and consequences (High, Medium, and Low)
-
Evaluate your controls (authentications, security, operations, administrative, and others)
-
Calculate the impact of risks, threats, and possibilities.
After step 5: Organizations can use a simulation model within the FAIR framework to analyze the probable financial impact of different risk scenarios, supporting more accurate and informed cybersecurity decisions. Continuous updates to risk assessments are necessary due to the dynamic nature of IT environments.
Nonetheless, mature risk-oriented organizations usually use the FAIR framework. A risk-first approach allows organizations to address broader risk categories and conduct in-depth analyses of external and internal risks.
FAIR Risk Assessment Checklist
For a company to run a FAIR risk assessment, it must go through four stages of risk quantification:
|
Stage |
Details |
|---|---|
|
Scenario Component Identification |
Two elements are at risk: an asset and the community. It is essential to identify the associated risk. Additionally, identify the relevant fair factors, threat communities, and primary stakeholders involved in the scenario. |
|
Loss Event Frequency Evaluation (LEF) |
LEF has sub-elements that need to be estimated. The following estimations are required: TCAP (Threat Capability), CS (Control Strength), TEF (Threat Event Frequency), Derive Vulnerability, and Derive LEF. Estimate threat event frequencies and consider each threat agent's capabilities and primary intent. |
|
Probable Loss Magnitude (PLM) |
PLM needs two estimates of elements onboard: the worst-case loss and the probable loss. Evaluate the probable magnitude of loss, organizational risk tolerance, and consider both secondary loss and secondary risks in the analysis. |
|
Articulate and Derive The Risk |
Once done with all the estimations, you can articulate and drive the risk. Analyze loss events and understand how these events contribute to a comprehensive risk assessment. |
Best Practices for FAIR Implementation
Successfully implementing the FAIR framework requires a thoughtful and systematic approach tailored to the organization’s unique risk profile and business goals. Best practices for FAIR implementation begin with clearly identifying and quantifying the risk scenarios most relevant to the organization. This involves analyzing and prioritizing risks based on their potential impact and likelihood, and developing targeted risk mitigation strategies to address the most significant threats. Establishing a comprehensive risk management framework—with well-defined policies, procedures, and controls—is essential for managing information risk effectively.
Additionally, organizations should invest in training and awareness programs to ensure that all employees understand the importance of information risk management and their role in managing risk. By following these best practices, organizations can maximize the value of the FAIR framework, enhance their ability to manage information risk, and build a culture of proactive risk management that supports long-term business success.
How to Utilize Data from the FAIR Risk Assessment?
When the assessment is completed, and you have calculated LEF, loss magnitude, and other parameters, you obtain the FAIR loss magnitude. It is a combination of primary and secondary losses, as secondary losses include penalties, customer loss, and damage to the brand. In contrast, primary losses include recovery costs, asset losses, and other direct losses.
The FAIR risk assessment method uses a confidence score for the security framework. Organizations can use the data obtained to improve their operating security framework by identifying gaps and reducing risks. Security professionals play a crucial role in interpreting FAIR assessment results and implementing necessary improvements. The company’s CISO can improve decision-making processes based on these KPIs, metrics, and results from the FAIR assessment.
Leverage a cybersecurity reporting tool, like CyberStrong, that streamlines the CISO or security leaders’ reporting requirements to secure executive interest and investment. Organizations that effectively use FAIR data to demonstrate risk reduction and improved decision-making can gain a competitive advantage in the market.
CyberStrong is Shaping the Cyber Risk Management Future
A FAIR risk assessment will deliver insights for risk scenario reporting, risk portfolio analysis and reporting. This risk assessment report will summarize the possible risks, the assets that face threats, and the potential financial loss because of the risks. These insights are crucial for C-level executives, board members, and non-technical business leaders. Ongoing risk assessments using FAIR support strategic decision-making by enabling organizations to move from static evaluations to continuous, automated risk management processes.
Not all organizational leaders are familiar with cybersecurity and risk terminologies. Frameworks other than FAIR provide complex insights that are challenging for non-technical members to understand, making decisions and organizational communication complex.
However, the data from FAIR presents the results in simple financial terms that decision-makers and team members can easily understand. The dollar loss can make anyone realize the severity of the risks and the prioritization of cybersecurity defensive measures. FAIR enables organizations to quantify risk by analyzing loss event frequency and loss magnitude, providing a clear, quantitative understanding of risk for more effective communication with stakeholders.
Furthermore, the organization can allocate its budget to cybersecurity and estimate the ROI on investment.
The CyberStrong platform allows simple automation for your data with cyber risk management and security frameworks. It reduces the complexity of framework testing with the FAIR risk methodology
Getting ready to evaluate CRQ vendors? Download our research brief on what to look for in cyber risk quantification software.
FAQ: Cyber Risk Quantification with FAIR
Q: What makes the FAIR model different from other risk assessment methods?
A: Unlike qualitative methods that rely on subjective scoring, the FAIR model provides quantitative, financial outputs. It calculates potential loss in dollar terms, making it easier for executives to understand and prioritize cyber risks.
Q: Who should use the FAIR model?
A: FAIR is ideal for CISOs, risk managers, and cyber risk analysts who need to communicate security posture to executive leadership and Boards in financial language that supports informed decision-making.
Q: Can the FAIR model work with other risk frameworks?
A: Yes. FAIR can be integrated with frameworks like NIST 800-30, and many platforms, including CyberStrong, support both. This hybrid approach allows organizations to tailor risk quantification to their maturity level.
Q: What kind of data is required to perform a FAIR analysis?
A: FAIR uses inputs like threat frequency, vulnerability data, and loss magnitude estimates. These can be sourced from historical incidents, industry benchmarks, or internal expert judgment.
Q: How often should a FAIR-based assessment be conducted?
A: Organizations should perform FAIR assessments regularly or whenever significant changes occur, such as system updates, new threats, or after implementing major controls, to keep ALE metrics current and relevant.
Wrapping Up
Your organizational data is at risk because it is highly valuable to cybercriminals. Utilize the FAIR model risk assessment to conduct systematic cyber risk quantification analyses to understand risk in financial terms, gain clear insights into your security posture, and effectively decide on measures to improve your cyber strategy.
Learn more about how you can quantify cyber risk with FAIR through CyberStrong or evaluate a NIST Cybersecurity Framework assessment tool.





.png)
.png)
.png)
%201.png)
.png)