- All
- Artificial Intelligence
- Audit Management
- Continuous Control Automation
- Corporate Compliance and Oversight
- Critical Infrastructure
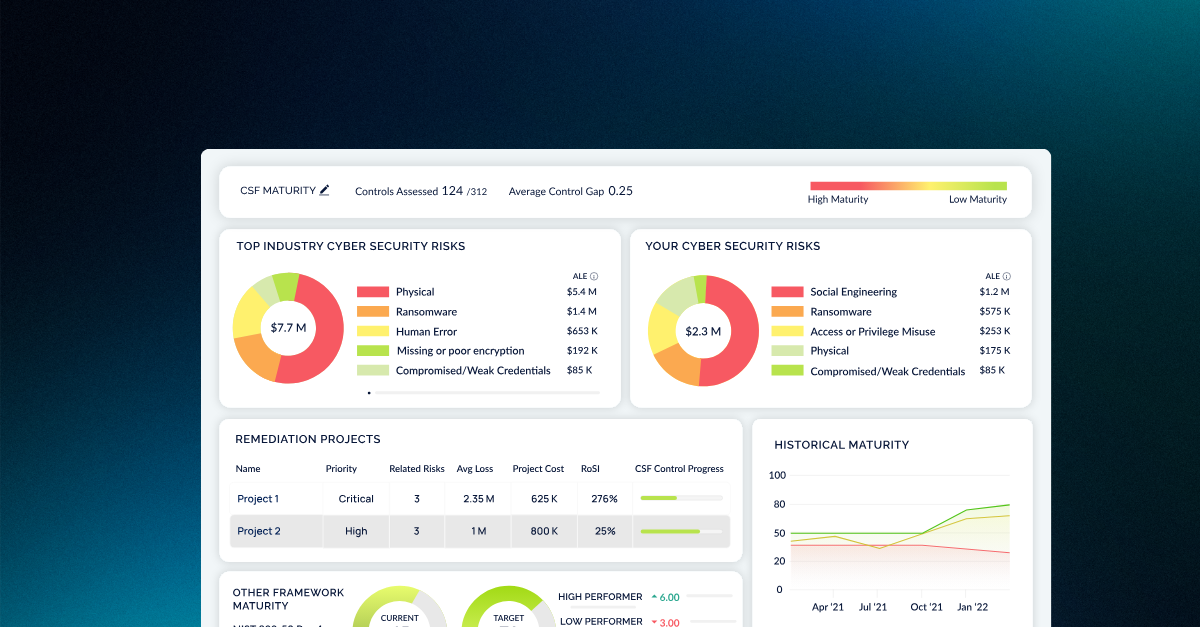
- Cyber Risk Management
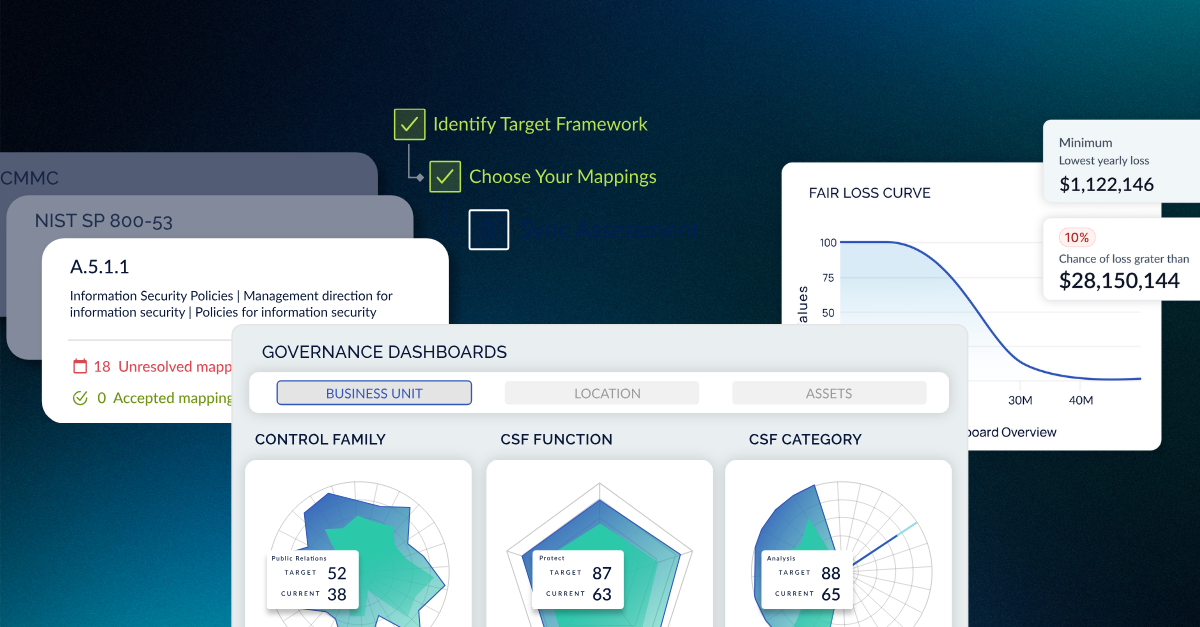
- Cyber Risk Management Frameworks
- Cyber Risk Quantification
- CyberSaint AI
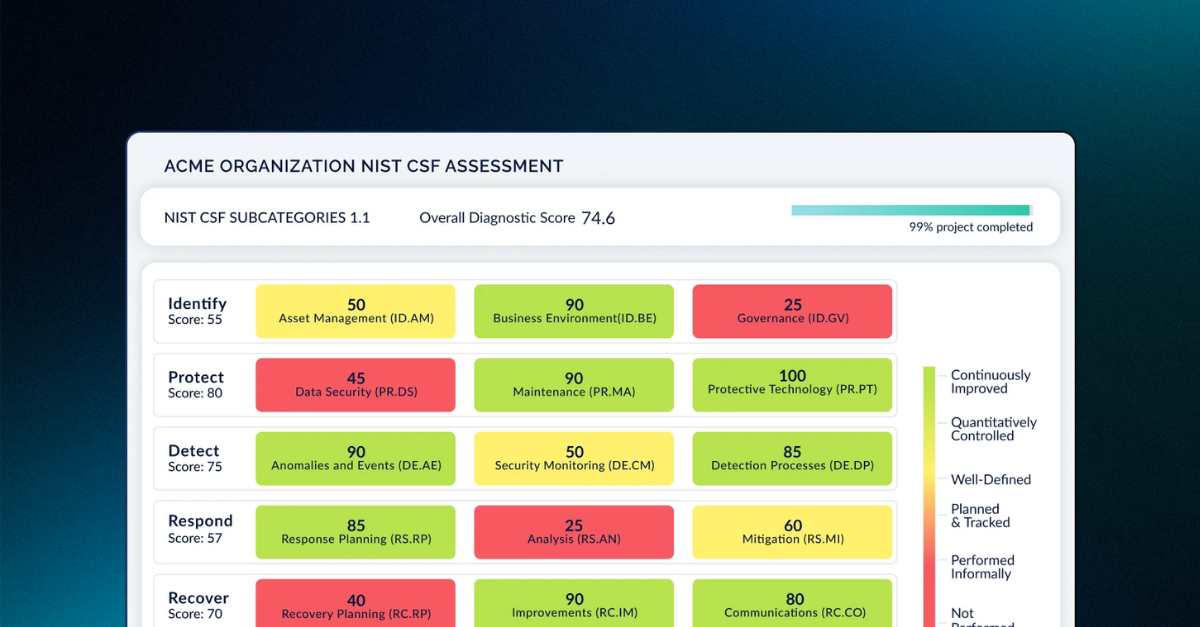
- CyberStrong
- CyberStrong Partner
- Cybersecurity Compliance Automation
- Cybersecurity Frameworks
- Cybersecurity Program Management
- Cybersecurity for Boards and CEOs
- DFARS
- Data Privacy
- Digital Risk Management
- Digital Transformation
- Energy & Utilities
- FAIR
- Financial Services
- Findings Management
- GDPR
- Healthcare
- ISO
- IT Risk Management
- Integrated Risk Management
- Manufacturing
- NIST Cybersecurity Framework
- NIST Privacy Framework
- NIST Risk Management Framework
- PCI
- Press Release
- Private Equity
- Product Updates
- STRONGER
- Small Business Cybersecurity
- Third-Party Risk Management
- Thought Leadership
- Vendor Risk Management
- implement
- product update