The Factor Analysis of Information Risk (FAIR) methodology breaks down risk into elements that organizations can compute, understand, analyze, and quantify cyber threats and their financial impact.
The FAIR model quantifies cyber threats and is equally effective in countering emerging risks, including operational risks.
Where Does FAIR Fall In The Greater Scheme Of Risk Assessments?
Many compliance models and management frameworks are available in the cyber security industry, like ISO 27001, NIST CSF, and COBIT. Their purpose is to ensure compliance and reduce enterprise risk. However, users have learned of gaps within these frameworks, which are like blind spots in their cyber risk management programs. These frameworks are valuable guiding structures, but a compliance-based approach cannot proactively manage risk. Security professionals must develop a risk-based approach that helps identify potential threats and measure risk in real time.
A FAIR risk assessment quantifies the risks arising from these gaps and presents them in terms of actual costs to people and processes. FAIR is an essential tool for organizations, as it breaks down risk into categories and estimates its potential financial impact. When cybersecurity teams and leaders clearly understand the types of threats, they can prioritize the needed actions and develop an effective risk management plan.
The FAIR model has become a game-changer in cybersecurity. Its ability to work simultaneously with other frameworks and efficiently streamline risk compliance, risk quantification, and risk assessment processes sets it apart from the rest.
How does FAIR Cybersecurity Risk Quantification Work?
The FAIR model consists of two primary components:
- Loss Event Frequency
- Loss Event Magnitude
According to the FAIR Institute, Loss Event Frequency is the probable frequency, within a given timeframe, that a threat actor will result in loss. This element describes the frequency at which a threat agent acts and, when they do act, how much loss a company might see.
- Threats related to assets (random, intentional, regular)
- Vulnerability of the targeted assets, whether they will be able to resist the threat
- The probability of action
Loss Magnitude is the measurement of the consequences of risk. Its components are:
- Primary losses include all the losses from an asset (its value, liability, volume, and productivity)
- Secondary losses include examining the internal and external factors that cause the loss of assets
Organizations prefer FAIR risk assessments, as they allow them to continuously quantify risk and identify the new gaps in the compliance frameworks, regardless of the organization's size and scalability. They can continue to expand and grow while implementing the FAIR model at every stage.
The FAIR risk model presents a realistic understanding of the financial impact of the risk measured. Many frameworks fail to deliver these results in monetary terms, leading organizations to underestimate risks and losses.
When leaders have an estimate of the financial impact, they can prioritize their threat response plans, allocate appropriate investments, and improve their decision-making. Moreover, it creates a transparent communication network within the organization.
How FAIR Data Helps Security Posture Management
The lack of relevant data is dangerous for the organization's cybersecurity. It affects the organization's operations, data security, and ability to make informed decisions. FAIR is an effective model for understanding the organization's cybersecurity goals and objectives.
Organizations can utilize their resources in the right direction and set their investment priorities straight. They can save significant time by working on the right metrics and data. The data obtained from the FAIR assessment provides an in-depth analysis of threats and consequences of risks.
Moreover, FAIR data makes budget allocation effective and the cybersecurity teams more efficient. FAIR model positively influences the organization's cybersecurity posture by optimizing the organization's cost and time factors.
Benefits of Understanding Risk in Financial Terms
Transparency is crucial in an organization’s communication network and risk management plan. FAIR helps security professionals understand the impact of existing gaps in the security posture, and can describe the impact of downtime.
The most significant advantage of the FAIR model is that it represents the results in financial terms. If organizations use anything other than economic or numerical terms to measure, it can be challenging to assess the true nature of risk and the threat it poses.
The organization gains many advantages when it has near-accurate data on the threats, risks, and possible financial losses. One such benefit is that internal and external communication improves. Leaders can make effective decisions and seamlessly share information and updates with board members, stakeholders, and team members.
The organization's daily operations and long-term goals depend on cybersecurity. Suppose an organization fails to reduce the gap in cybersecurity and business function. It can create panic during a cyber-attack, and employees will be partially or unaware of the emergency protocols. A cyberattack of this scale can result in significant losses of money, reputation, and goodwill.
Board members, leaders, and CISOs can draft protocols and policies using FAIR to ensure the organization's long-term goals are met and data is protected. The measures will also affect the ROI, investment, and business operations.
CyberSaint is Leading CRQ for Enterprises
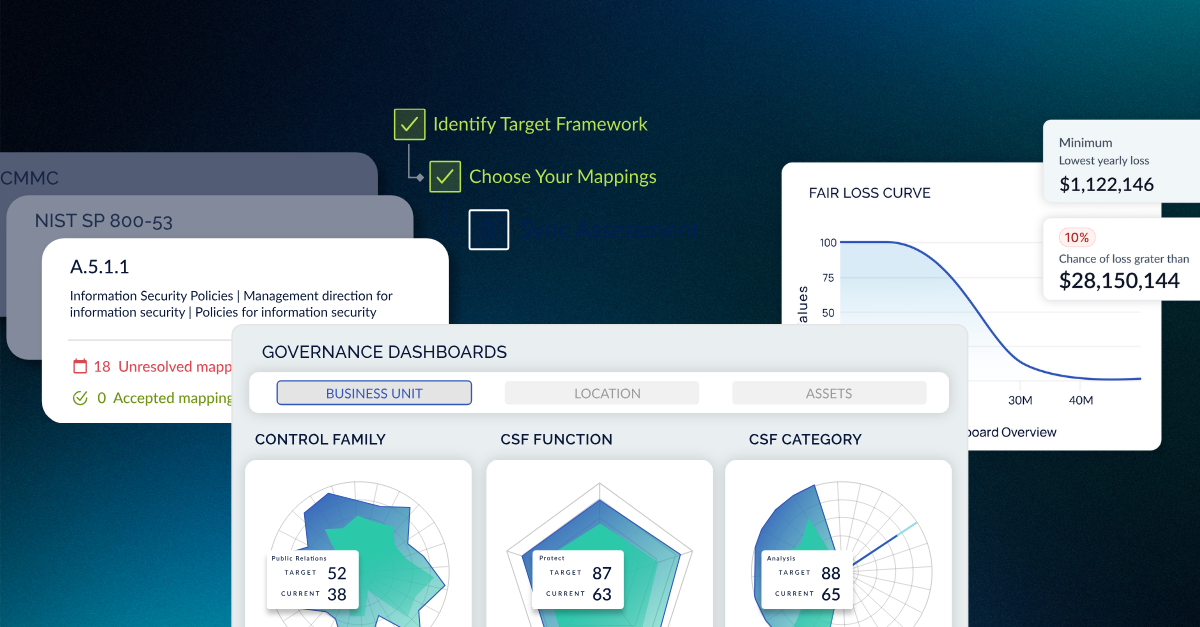
Using the latest technology and automation ensures your cybersecurity is always informed and prepared. CyberStrong enables you to simultaneously automate multiple frameworks like NIST, ISO, and FAIR. It also provides detailed insights on risk management and quantification.





.png)
.png)
.png)
%201.png)
.png)