Has anyone ever been the victim of a data breach? I have, and it’s not a pleasant experience. For some, it’s as simple as getting a new credit or debit card, but for others, it can go much deeper. Your personal information and finances could be at risk, or even your identity. This could also mean access to confidential business information, like trade secrets or intellectual property. Imagine this breach happened to a federal organization handling vital information about the United States.
Data breaches have been an issue long before technology. A data breach refers to any confirmed incident in which sensitive, confidential, or otherwise protected data has been accessed or disclosed unauthorizedly. As technology grew, so did the risk of data breaches. Breaches plagued the early 2000s. In January of 2000, CD Universe, an online music store, was hacked, and 300,000 customer credit cards were compromised. 25,000 stolen credit card numbers were then posted online. Egghead.com suffered a massive breach that affected 3.5 million users. The hacker then held the company’s information for ransom, demanding $100,000. Later that year, AOL and Western Union were also victims of breaches.
An Overview of the NIST 800-53 Framework
For organizations that haven’t experienced this, thank the E-Government Act of 2002 or, more specifically, the Federal Information Security Management Act or FISMA. Passed on December 17th, 2002, this act directed the National Institute of Standards and Technology (NIST) regulatory agency to develop guidelines to heighten the security of information systems used within the federal government. Helping reduce the risk of cyberattacks on critical infrastructure. Why is this important, you might ask? We now refer to these guidelines as the NIST Special Publication (SP) 800-53.
With breaches and hackers becoming front-page news, action must be taken to protect and secure vital information. This prompted the E-Government Act, effectively creating the NIST 800-53. The NIST Special Publication 800-53, Security and Privacy Controls for Information Systems and Organizations, is a set of recommended security and privacy controls for federal information systems and organizations to help meet the Federal Information Security Management Act (FISMA) requirements. It aims to improve your organization’s information systems security program by providing controls supporting the development of secure and resilient federal information systems.
What is NIST 800-53?
NIST SP 800-53 provides a list of controls that support the development of secure and resilient federal information systems. These controls are the operational, technical, and management standards and guidelines information systems use to maintain confidentiality, integrity, and availability. The guidelines adopt a multi-tier approach to risk management through control compliance. NIST 800-53 control families are broken into three classes: low, moderate, and high, and are based on impact. The controls are split into 18 security control families, allowing organizations to select only the most applicable to their requirements. NIST SP 800-53 introduces baselines as a starting point for the control selection process. This enables organizations to establish a baseline for developing secure organizational infrastructure.
All U.S. federal government agencies and contractors must comply with NIST SP 800‐53; however, many state and local governments and private organizations use NIST SP 800‐53 as their security controls framework.
Why wouldn't you if the federal government trusts NIST SP 800-53 to protect its critical data? The guidelines are revised following the evolving nature of managing information security and covering areas like mobile and cloud computing, insider threats, application security requirements, and supply chain security standards. This helps you future-proof as technology evolves, as well as your business.
Learn about NIST 800-53 Rev 5 here.
NIST 800-171 vs. NIST 800-53
NIST 800-171 and NIST 800-53 are cybersecurity standards developed by NIST, but they serve different purposes and target different audiences.
NIST 800-171 focuses on protecting sensitive federal information in non-federal systems. It provides guidelines for safeguarding Controlled Unclassified Information (CUI) in these environments. On the other hand, NIST 800-53 offers a comprehensive framework of controls to secure federal information systems. This standard is broader in scope, encompassing a wide range of security and privacy controls intended for federal agencies and organizations that interact with federal systems. While NIST 800-171 is more prescriptive and tailored to specific data types, NIST 800-53 provides a more extensive and flexible set of controls adaptable to various information security needs.
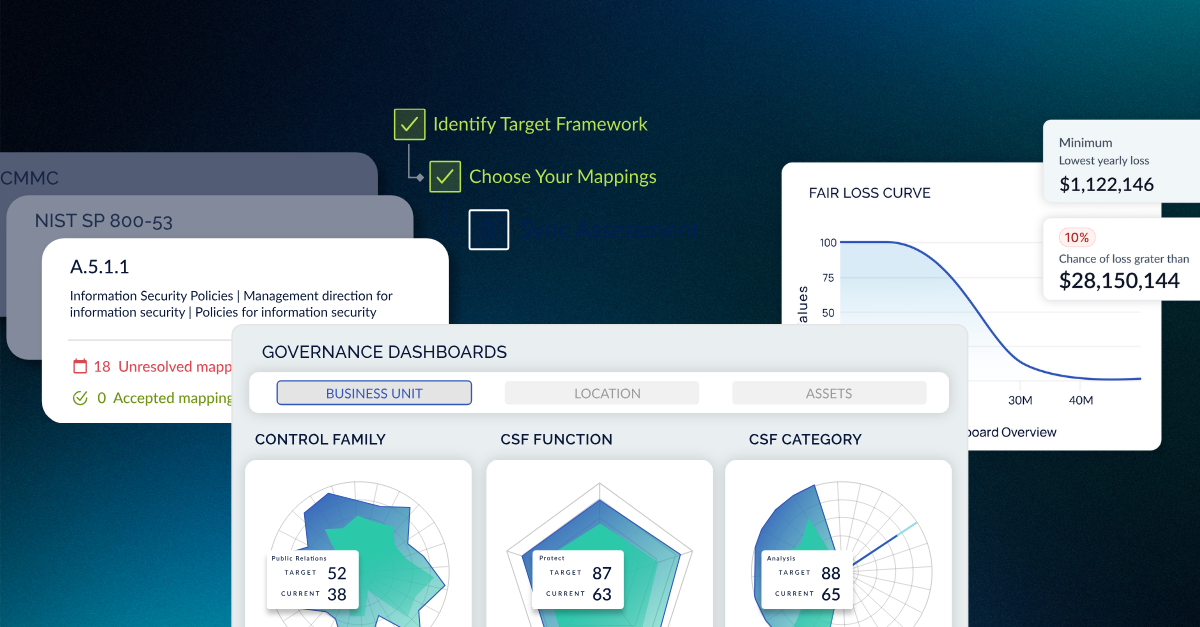
Protect yourself and ensure the security of your organization’s critical information. At CyberSaint, we support numerous frameworks, such as the NIST SP 800-53, Top 18 CIS Controls, SOX, and many other gold-standard frameworks and controls. The NIST CSF establishes a fundamental baseline for developing secure organizational infrastructure, improving your organization’s information systems, and risk management in cybersecurity.





.png)
.png)
.png)
%201.png)
.png)