The National Institute of Standards and Technology (NIST) is responsible for developing the NIST Cybersecurity Framework (CSF), the gold standard cybersecurity framework. NIST Special Publication 800-53 operates as one of the forefront cybersecurity guidelines for federal agencies in the United States to maintain their information security systems. These guidelines protect the system's security and the sensitive data of the citizens being served.
How Many Control Families are in NIST 800-53?
NIST SP 800-53 has had five revisions and comprises over 1000 controls. This catalog of security controls allows federal government agencies to recommend security and privacy controls for federal information systems and organizations to protect against potential security issues and cyber attacks. Here, we will look at the 18 NIST 800-53 control families and give a general overview of the list of NIST standards.
List of NIST 800-53 Control Families
AC - Access Control
The AC Control Family consists of security requirements detailing system logging. This includes who has access to what assets and reporting capabilities like account management, system privileges, and remote access logging to determine when users can access the system and their level of access.
AU - Audit and Accountability
The AU control family comprises security controls related to an organization’s audit capabilities. This includes audit policies and procedures, audit logging, audit report generation, and protection of audit information.
AT - Awareness and Training
The control sets in the AT Control Family are specific to your security training and procedures, including security training records.
CM - Configuration Management
CM controls are specific to an organization’s configuration management policies. These include a baseline configuration that will operate as the basis for future builds or changes to information systems, information system component inventories, and a security impact analysis control.
CP - Contingency Planning
The CP control family includes controls specific to an organization's contingency plan in case a cybersecurity event should occur. These include controls like contingency plan testing, updating, training, backups, and system reconstitution.
IA - Identification and Authentication
IA controls are specific to an organization's identification and authentication policies. This includes the identification and authentication of organizational and non-organizational users and the management of those systems.
IR - Incident Response
IR controls are specific to an organization’s incident response policies and procedures. This includes incident response training, testing, monitoring, reporting, and response plans.
MA - Maintenance
The MA controls in NIST 800-53 revision five detail requirements for maintaining organizational systems and the tools used.
MP - Media Protection
The Media Protection control family includes controls specific to access, marking, storage, transport policies, sanitization, and defined organizational media use.
PS - Personnel Security
PS controls relate to how an organization protects its personnel through position risk, personnel screening, termination, transfers, sanctions, and access agreements.
PE - Physical and Environmental Protection
The Physical and Environmental Protection control family is implemented to protect systems, buildings, and supporting infrastructure against physical threats. These controls include physical access authorizations, monitoring, visitor records, emergency shutoff, power, lighting, fire protection, and water damage protection.
PL - Planning
The NIST SP 800-53 control PL family is specific to an organization's security planning policies and must address the purpose, scope, roles, responsibilities, management commitment, coordination among entities, and organizational compliance.
PM - Program Management
The PM control family is specific to who manages your cybersecurity program and how it operates. This includes but is not limited to a critical infrastructure plan, an information security program plan, a plan of action, milestones and processes, a risk management strategy, and enterprise architecture.
RA - Risk Assessment
The RA control family relates to an organization’s risk assessment policies and vulnerability scanning capabilities. An integrated cyber risk management solution like CyberStrong can help streamline and automate your NIST 800 53 compliance efforts.
CA - Security Assessment and Authorization
The Security Assessment and Authorization control family includes controls that supplement the execution of cybersecurity assessments, authorizations, continuous monitoring, plans of action and milestones, and system interconnections.
SC - System and Communications Protection
The SC control family is responsible for systems and communications protection procedures. This includes boundary protection, protection of information at rest, collaborative computing devices, cryptographic protection, denial of service protection, and many others.
SI - System and Information Integrity
The SI control family correlates to controls that protect the system and information integrity. This control family includes NIST SI 7, which involves flaw remediation, malicious code protection, information system monitoring, security alerts, software, firmware integrity, and spam protection.
SA - System and Services Acquisition
The SA control family correlates with controls that protect allocated resources and an organization’s system development life cycle. This includes information system documentation controls, development configuration management controls, and developer security testing and evaluation controls.
How Many Controls are in NIST 800-53 Rev 4?
NIST SSP 800-53 Rev 4 contains a total of 256 controls. These controls are organized into 18 families, each addressing a specific aspect of cybersecurity and privacy. The control families cover various areas such as Access Control, Audit and Accountability, Incident Response, and System and Information Integrity.
The controls are further categorized based on the impact level of the information systems:
- Low-impact systems: 115 controls and 9 enhancements
- Moderate-impact systems: 159 controls and 102 enhancements
- High-impact systems: 170 controls and 173 enhancements
How Many Control Families are in NIST 800-53 Rev 5?
NIST Special Publication 800-53 Revision 5 contains over 1,000 controls. Specifically, it comprises:- 1,077 controls
- 1,207 enhancements
- Thousands of additional steps for implementing these controls
The controls are organized into 20 control families. However, it's important to note that the number of controls in each baseline has changed from Revision 4 to Revision 5:
High baseline: Decreased from 421 to 392 controls
Moderate baseline: Decreased from 325 to 304 controls
Low baseline: Increased to 150 controls
What is the Difference Between CMMC and NIST 800-53?
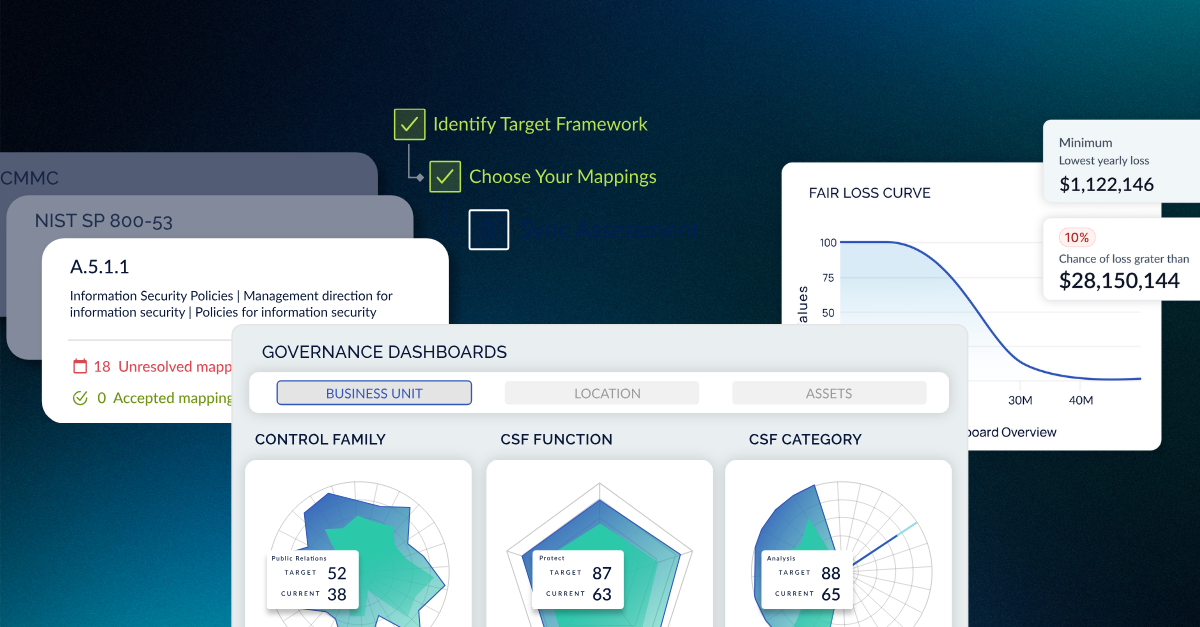
Cybersecurity Maturity Model Certification (CMMC) and NIST 800-53 are related but distinct cybersecurity frameworks with different purposes and scopes. While NIST 800-53 provides a comprehensive set of over 1,000 security controls for federal information systems, CMMC is a more focused framework designed specifically for Department of Defense (DoD) contractors handling Controlled Unclassified Information (CUI). CMMC builds upon the foundation of NIST 800-53, with almost every CMMC mapping to a NIST 800-53 control.
The key differences lie in their certification processes, structure, and mandatory nature. CMMC requires third-party assessment and certification, uses a maturity model approach with three levels, and is a contractual requirement for DoD contractors. In contrast, NIST 800-53 compliance is typically verified through self-assessment or independent attestation, uses three baselines based on risk profile, and is mandatory for federal agencies but not for contractors. Despite these differences, the two frameworks are closely related and mapped to each other, meaning organizations implementing NIST 800-53 controls will find themselves well-positioned to meet CMMC requirements.
How are FedRAMP Control Families related to NIST 800-53?
FedRAMP and NIST 800-53 are closely related yet distinct cybersecurity frameworks. FedRAMP leverages NIST 800-53 as its baseline for security controls, adopting and adapting them to the cloud context. While NIST 800-53 provides a comprehensive catalog of security and privacy controls for all types of information systems, FedRAMP focuses specifically on cloud services and offers a standardized approach for assessing and authorizing cloud products. NIST 800-53 is mandatory for federal agencies and organizations working with federal systems, but can be used by any organization, whereas FedRAMP applies specifically to cloud service providers seeking to work with federal agencies. In terms of implementation, NIST 800-53 offers flexibility in control selection based on an organization's risk assessment, while FedRAMP provides more specific requirements for cloud environments.
Additionally, FedRAMP offers a standardized assessment and authorization process for cloud services, whereas NIST 800-53 is part of the general risk management framework for federal information systems. Despite these differences, implementing NIST 800-53 controls often helps organizations meet FedRAMP requirements due to their close alignment, as both frameworks aim to enhance the security posture of information systems used by the federal government.
How are the NIST RMF Control Families related?
The NIST Risk Management Framework (RMF) and NIST 800-53 control families are closely related components of a comprehensive cybersecurity strategy. While NIST 800-53 provides a catalog of security and privacy controls organized into 20 families, the RMF offers a structured process for implementing these controls. The RMF guides organizations through steps like preparation, categorization, selection, implementation, assessment, authorization, and monitoring of security controls. Essentially, the RMF provides the methodology for how to effectively apply the NIST 800-53 control families within an organization's risk management context. Together, they form a robust approach to identifying, implementing, and managing cybersecurity measures across an organization's information systems.
A cyber risk management solution like CyberStrong can help streamline and harmonize an organization's cybersecurity efforts across multiple standards and guidelines, saving teams time, energy, and resources to comply continuously.
If you have questions about NIST SP 800 53, the NIST Cybersecurity Framework, cyber risk management, or how CyberStrong enables regulatory agencies to streamline and automate their compliance efforts, click here to schedule a conversation.
NIS2 is a growing requirement for organizations of all sizes and maturity. Get the latest insights on the NIS2 Directive Resources.





.png)
.png)
.png)
%201.png)
.png)