@BoozAllen @BoozAllenCyber #cybertrends #cybersecurity #cyber Find out the 8 ways threat actors can make waves in 2019 in the annual Booz Allen Cyber Threat Outlook Report: https://t.co/IdmCKC6Rev
— Heather A. Holdaway (@tenshicrow83) February 5, 2019
Security Experts Comments:
George Wrenn, CEO at CyberSaint:
 “Cyber defense will only evolve, and must evolve, with technology and the increasing risks we see in this heavily digital era. The key risk areas identified in this report- IoT, Social Media, Business Leadership- are evidence that digital risk management isn’t just a cybersecurity issue, and as many of us know, cybersecurity isn’t just a technical issue anymore.
“Cyber defense will only evolve, and must evolve, with technology and the increasing risks we see in this heavily digital era. The key risk areas identified in this report- IoT, Social Media, Business Leadership- are evidence that digital risk management isn’t just a cybersecurity issue, and as many of us know, cybersecurity isn’t just a technical issue anymore.
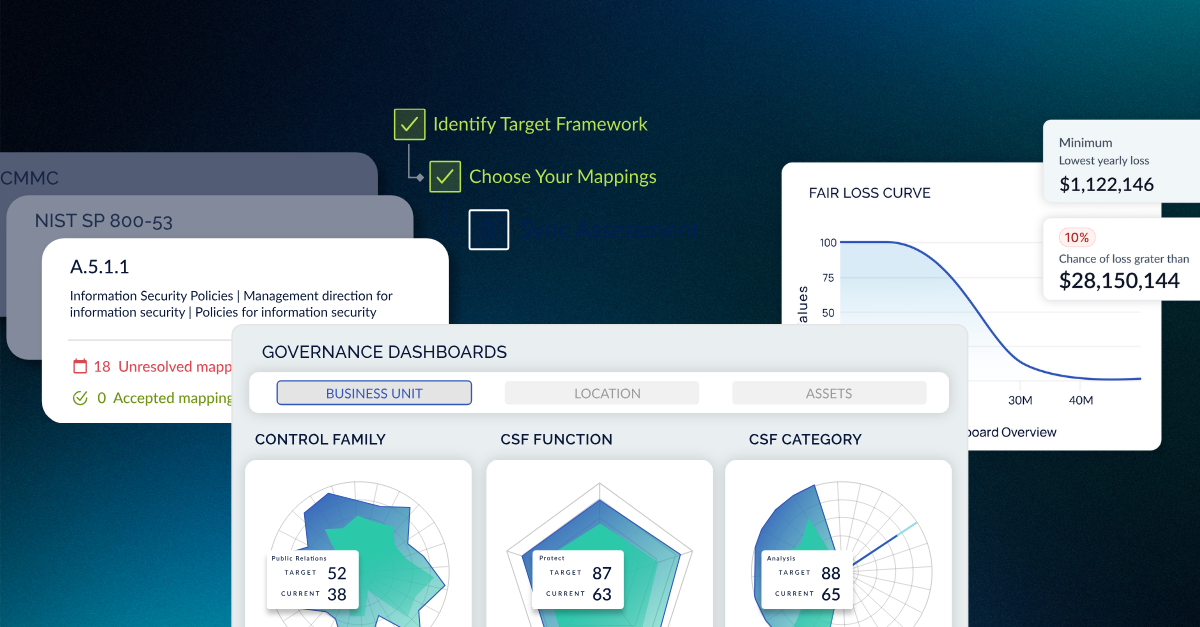
Leadership that understands how to approach risk management on a continual basis, in a way that connects all business unity and not simply engages the cybersecurity unit, is key. Even better is implementing technology to help link relevant threats to live controls across business assets, which allows for prioritization, efficiency, effective remediation and therefore more resilience.”
Pravin Kothari, CEO at CipherCloud:
 “Booz Allen’s new cyber report highlights key threat areas for 2019. Most interesting is the focus on internet of things (IoT) devices as a high risk area. The Booz Allen report brings focus to the open vulnerabilities in these devices. You may be aware that a recently passed California law SB-327 requires any manufacturer of an IoT device must ship with a unique password as of January 1, 2020. No more default passwords! As California goes, so goes the United States so this law will have broad impact. IoT devices are also very difficult to defend as most customers have no real visibility into IoT operations. Assuming malware or an attacker back-door has been detected, it is also almost impossible to clean the devices.
“Booz Allen’s new cyber report highlights key threat areas for 2019. Most interesting is the focus on internet of things (IoT) devices as a high risk area. The Booz Allen report brings focus to the open vulnerabilities in these devices. You may be aware that a recently passed California law SB-327 requires any manufacturer of an IoT device must ship with a unique password as of January 1, 2020. No more default passwords! As California goes, so goes the United States so this law will have broad impact. IoT devices are also very difficult to defend as most customers have no real visibility into IoT operations. Assuming malware or an attacker back-door has been detected, it is also almost impossible to clean the devices.
Another area the Booz Allen report highlights is that of information warfare leveraged by the power of social media and malign websites. Increasingly, nation-states and other entities use the power of social media to support information warfare campaigns. Social media can be deployed as a cannon of misinformation to damage corporate reputations, attack government institutions and their policies, attack individual politicians and organizations, and in general obfuscate the truth and confuse the public.”
This post originally appeared on Information Security Buzz, read the original post here.