Modern organizations operate in environments where cyber risks evolve daily, cloud infrastructure changes continuously, and compliance expectations intensify across jurisdictions. In this environment, traditional risk management that relies on static risk assessments and manual effort is no longer sufficient.
Operationalizing risk means transforming risk management from a periodic communication exercise into a dynamic, intelligence-driven discipline. It requires continuous monitoring, real-time data integration, and automated discovery of new risks as they emerge across systems. Organizations that implement continuous risk monitoring gain real-time insights into their security posture and are better positioned to make risk-based decisions aligned with business goals.
This shift is foundational to strengthening the cybersecurity posture, improving compliance, and enabling organizations to stay ahead of regulatory changes and evolving cyber risks.
Why Manual Compliance & Risk Processes Cannot Scale
Many organizations still depend on annual spreadsheet-based risk assessments and manual control reviews. This traditional risk management approach creates significant friction in security processes, delaying analysis and reporting.
Manual risk management processes typically involve:
- Gathering security data from multiple tools
- Reconciling compliance obligations in a point-in-time fashion
- Updating risk scores periodically rather than continuously
- Preparing documentation for audits and audit prep cycles
- Coordinating follow-up activities across distributed risk teams
This approach creates several structural limitations.
- First, risk identification becomes episodic rather than ongoing.
- Second, compliance status may appear stable while underlying security risks change.
- Third, risk managers and security teams spend disproportionate time on documentation instead of strengthening the cybersecurity program.
In cloud infrastructure environments, configurations can shift within hours. New workloads introduce potential risks. Access permissions change frequently. Without continuous monitoring, organizations lack visibility into evolving security risks. Static risk assessments cannot reflect these rapid changes in data flow, infrastructure, and application behavior.
As cyber threats accelerate and artificial intelligence increases attacker sophistication, reliance on periodic reviews places organizations at a disadvantage. Risk managers need continuous risk signals derived from accurate data, not retrospective summaries. Continuous compliance automation helps organizations maintain regulatory standards without excessive manual input.
From Static Risk Assessments to Continuous Risk Monitoring
Traditional risk assessments are still important, but they should serve as strategic checkpoints rather than the primary mechanism for risk management. Continuous risk monitoring ensures that the security posture reflects current operating conditions rather than outdated documentation.
Continuous monitoring integrates security data across existing assets and centralizes it on a single platform for real-time visibility. Increased efficiency is achieved by reducing manual reporting efforts and focusing on strategic analysis. This allows teams to:
- Detect new issues as soon as they emerge
- Monitor risks dynamically
- Track trends over time
- Align security initiatives with measurable risk reduction
- Support informed decisions based on current exposure
By combining automated discovery with behavioral analytics and threat intelligence, organizations gain deeper analysis of evolving cyber threats. Instead of reacting to data breaches or audit findings, they move toward proactive security strategies. Continuous compliance automation simplifies audits and streamlines communication processes. Layer on CRQ on top of continuous risk monitoring, and insights abound. By calculating financial scenarios like Annualized Loss Expectancy (ALE), organizations can make informed decisions about risk transfer and mitigation.
This approach also enhances third-party risk management. Vendors introduce potential risks that may affect critical assets and data flows. Continuous monitoring of TPRM programs provides earlier visibility into supplier-related security risks and compliance obligations.
Overall, organizations that leverage compliance automation see a direct impact: lower costs and improved resilience.
How to Embed Cyber Risk into Daily Security Operations
Operationalizing cyber risk means integrating risk management directly into daily security operations rather than isolating it within compliance functions.
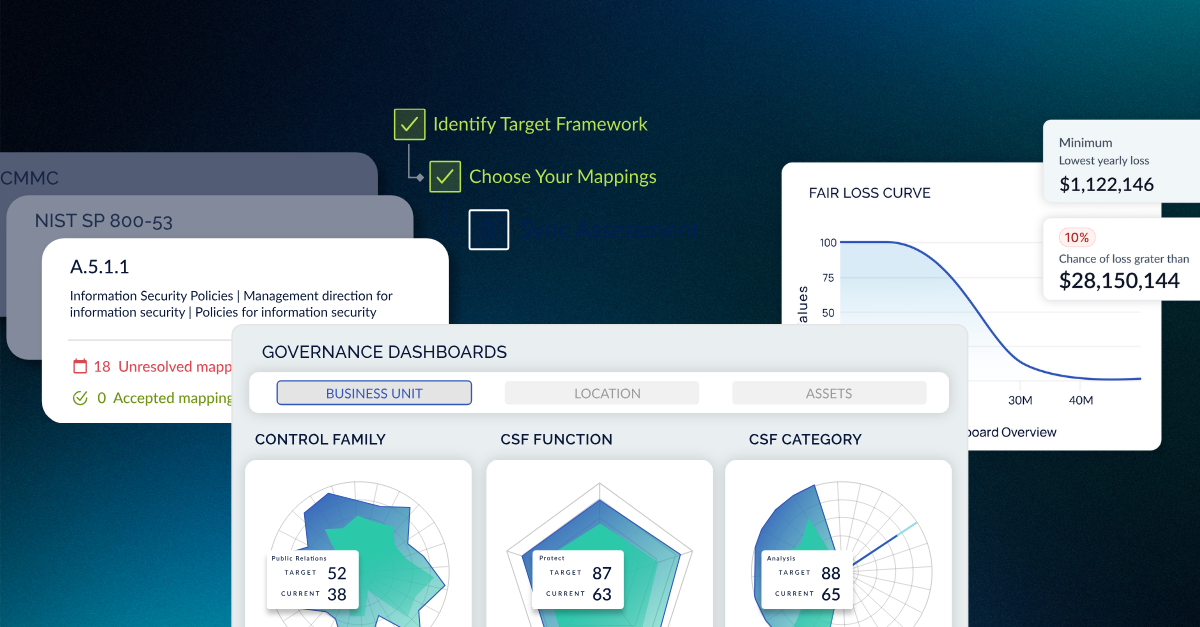
An effective cyber risk automation platform ingests security data from across the enterprise and maps it against compliance requirements, security controls, and business goals. This enables organizations to centralize reporting in a unified system that provides real-time insights across the security program. Centralized dashboards integrate data from across departments into a single, visible interface, providing an overview of the risk landscape.
Within an operationalized model:
- Continuous monitoring evaluates security posture across infrastructure and on-prem systems
- AI-powered findings management identifies new issues and gaps as environments evolve
- Threat intelligence feeds enhance the analysis of emerging cyber risks
- Risk assessment processes update risk scores dynamically
- Compliance status updates automatically as controls change
This model reduces manual hours and allows security teams to focus on strengthening defenses rather than assembling audit artifacts.
Risk teams gain valuable insights into how security investments reduce exposure over time. Leadership gains clarity into cyber posture across units. Executives can make more informed decisions grounded in real-time data rather than retrospective analysis.
Automation Enables Continuous & Connected Cyber Risk
Automation is the enabling force behind continuous monitoring. A modern, AI-powered cyber risk management platform integrates AI, behavioral analytics, and automated findings to scale analysis across complex environments.
Automation allows organizations to:
- Aggregate security data across existing tools
- Normalize control data into structured risk scores
- Monitor data between systems
- Detect deviations from security policies
- Support ensuring regulatory compliance through automated control validation
AI enhances the identification of anomalous behaviors, while behavioral analytics surfaces subtle insights that traditional processes may overlook. This capability is increasingly crucial as nation-states leverage AI-powered attack techniques.
Automation also supports proactive incident management by detecting control drift before data breaches occur. When integrated with threat intelligence feeds, the platform can correlate emerging threats with internal exposure levels and adjust risk objectives accordingly.
By eliminating manual work from routine monitoring and reporting processes, organizations free risk teams to focus on higher-value risk management strategies and security initiatives.
How to Strengthen Compliance and Audit Prep with Continuous Monitoring
Regulatory compliance remains a core driver of enterprise risk management. However, compliance requirements are expanding globally, and regulatory shifts occur frequently. Organizations need to show compliance, effective risk assessments, and a strong risk culture.
Continuous monitoring strengthens regulatory compliance by maintaining up-to-date evidence across controls. It is the real-time process of identifying, assessing, and mitigating issues before they seriously damage an organization's operations, profitability, reputation, or compliance. Instead of conducting intensive audit prep cycles before audits, organizations maintain a steady state of readiness.
Continuous Compliance Automation supports:
- Ongoing assessment of compliance posture
- Mapping of security controls to compliance requirements
- Centralized reporting for audits
- Documentation of follow-up remediation activities
This model strengthens credibility with regulators by demonstrating systematic risk management practices rather than episodic review processes.
4 Ways Automation Enhances Risk-Based Decision Making
Operationalized enterprise risk management aligns security posture with business objectives. When security data is contextualized through analysis and centralized reporting, leadership can prioritize investments based on measurable impact.
Continuous risk monitoring enables:
- Identification of critical assets requiring additional protection
- Evaluation of security workstreams against changing risk levels
- Allocation of security investments based on quantified exposure
- Alignment of security teams and risk teams around shared goals
This approach enables risk-based decision-making enterprise-wide. Successful continuous risk monitoring requires executive buy-in and leadership commitment. Organizations should prioritize risk management strategies that materially reduce business issues, rather than focusing only on compliance checklists.
More informed decisions emerge when executives have real-time views into how security posture evolves. Building a risk-aware culture means cyber isn't seen as someone else's job, and regular feedback sessions keep everyone engaged.
From Fragmented Tools to an Automation-First Cyber Risk Management Platform
Many organizations rely on numerous security tools that generate isolated data streams. Without integration, these existing tools create fragmented visibility and duplicate processes.
A single platform that consolidates monitoring, reporting, automated discovery, and compliance mapping allows organizations to move a step ahead of reactive risk management. Centralized reports aggregate assessment data into actionable intelligence.
Such a platform must be able to continuously monitor infrastructure, applications, and cloud environments; integrate threat intelligence with behavioral analytics; automatically surface and prioritize new findings; process and correlate data in real time; deliver centralized, role-based dashboards and reporting; and scale to support audits, regulatory obligations, and ongoing compliance programs.By unifying data flows, organizations eliminate silos and strengthen cybersecurity maturity.
Leveraging Proactive Risk Management as a Competitive Advantage
Organizations that embrace proactive risk management strategies position themselves a step ahead of evolving cyber risks. Rather than responding to data breaches or regulatory enforcement actions, they operate with continuous visibility.
Proactive cyber risk management offers several measurable benefits, including a reduced likelihood of data breaches, faster detection of security risks, and improved audit outcomes. It also fosters greater alignment between security initiatives and overall business objectives, enhancing trust among regulators, customers, and partners.
In highly regulated industries, the ability to demonstrate continuous risk monitoring and real-time cyber risk visibility can serve as a competitive differentiator.
Cyber risk management is not a back-office compliance function. It is a strategic discipline that informs business strategy, supports compliance, and protects critical assets.
Organizations that operationalize risk through AI-powered automation, CCM, and centralized reporting transform their security organization from reactive to proactive. They reduce manual effort, strengthen risk identification processes, and enable organizations to make more informed decisions grounded in real-time reports. Organizations that leverage compliance automation also see lower costs and greater resilience against cyber threats.
As regulatory changes accelerate and bad actors become more sophisticated, the question is no longer whether to modernize risk management practices, but how. Leveraging AI-powered automation at CISOs' disposal enhances risk quantification by translating cyber risk into financial impact metrics.
The question now is how quickly organizations can embed continuous monitoring, automated findings identification, and integrated analysis into a unified cyber risk automation platform that delivers sustainable real-time cyber risk visibility.





.png)
.png)
.png)
%201.png)
.png)