In 2017 the New York State Department of Financial Services (NYDFS) created the NYDFS cybersecurity regulation 23 NYCRR 500, which held financial institutions accountable for maintaining their cybersecurity program. These regulation requirements, heavily based on the NIST Cybersecurity Framework, demand regulated entities to assess their cybersecurity risk and proactively improve them, while allowing for flexibility based on a financial institution's needs, scope, and influence. To comply with New York Department of Financial Services cybersecurity regulations, organizations will need to maintain cybersecurity obligations continuously. As the threat of data breaches and cyber attacks grows by the day, so does the need for regulation to protect organizations and provide a measurable standard of operation.
The NYDFS cybersecurity regulation applies to any financial institution in operation under NYDFS licensure, including:
- State banks
- Licensed Lenders
- Private Banks
- Foreign Banks operating in New York
- Mortgage Companies
- Insurance companies
- Trust companies
- Service providers
The 23 NYCRR 500 regulation includes limited exemptions for financial institutions with less than ten employees and less than 5 million in gross annual revenue in the past three years. Additionally, institutions that do not have any nonpublic information or sensitive data are also entitled to certain exemptions.
Proving Compliance with NYDFS
Taking influence from the NIST CSF, NYDFS is requiring companies to develop a data security policy and implement an incident response plan that includes a notification system for data breaches and cybersecurity events within 72 hours. Under this NYDFS regulation, a program must coincide with best practices that support:
- Information Security
- Access Controls and identity management
- Business continuity and disaster recovery planning
- Security and Personnel Training
- Security of information systems
- Network Security
- Periodic risk assessments
- Internal reporting and auditing
- Data Encryption and Protection
- Threat Feed Detection
- Incident Response Plans
- Multi-Factor Authentication
- Vendor/ Third-Party Risk Assessments
Utilizing risk assessments to benchmark and assess the posture of your cybersecurity program is essential. At the end of each year, financial institutions need to complete an annual certification process in coordination with the board of directors to evaluate their cybersecurity program. At the end of this process, the organization will need to provide a Certification of Compliance with NYDFS Cybersecurity Regulation.
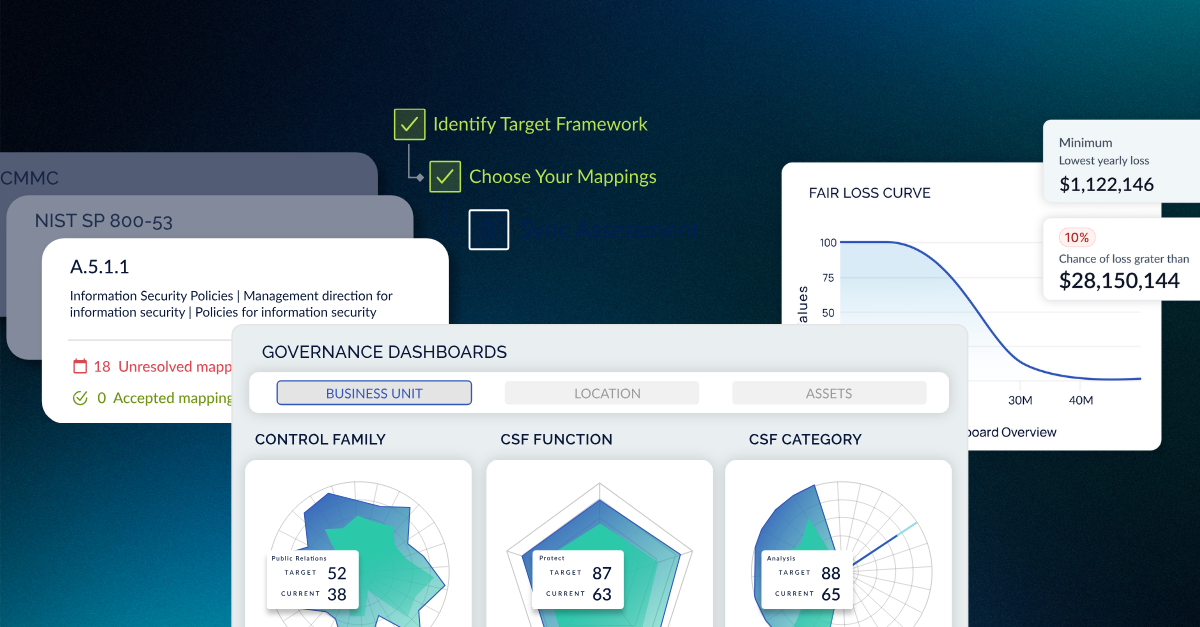
Utilizing an integrated risk management platform like CyberStrong can help streamline this process and many other gold standard frameworks. Integrated risk management can centralize compliance efforts, saving cybersecurity teams and Chief Information Security Officers (CISOs) valuable time, energy, and resources, bridging the gap between cybersecurity and the board to fully translate the importance of the organization’s cybersecurity needs. By integrating dashboards, patented AI, and groundbreaking reporting into your cybersecurity program, you can prove your compliance with NYDFS cybersecurity regulations and multiple other custom frameworks and controls with an audit trail in hours instead of days.
If you have any additional questions about integrated risk management or how CyberStrong can help bolster your institution’s cybersecurity objectives, give us a call at 1 800 NIST CSF or click here and request a free demo.





.png)
.png)
.png)
%201.png)
.png)